Real Names, Fake IDs, and a Bank Insider: The Massachusetts Fraud Ring That Beat Two Lines of Defense

Picture a stranger walking into your bank branch and asking to withdraw from your account. They slide a photo ID across the counter.
Your name is on it.
Your date of birth matches.
Your Social Security number checks out.
The only thing that is wrong is the face, which belongs to someone you have never met.
This is exactly what happened to customers at banks across Massachusetts, Connecticut, and Rhode Island for years.
On May 2, 2026, Victor Kolawole, 26, of Brockton, and Keith Wainaina, 24, of Lowell, pleaded guilty in federal court to bank fraud, conspiracy to commit bank fraud, and conspiracy to commit money laundering. A third co-conspirator, Phalentz Vernot, pleaded guilty in December 2025.
Six men were arrested in total as part of the same investigation.
Their scheme had two essential ingredients: stolen customer PII, and bank employees willing to look the other way. When those two elements combined with convincing fake IDs, the fraud ran for years before federal prosecutors caught up with it.
How the scheme worked
The operation started from the inside.
Vernot had access to customer records at the targeted banks, and he used that access to pull real account holder information: names, dates of birth, Social Security numbers, and account numbers. Armed with that data, he and Wainaina recruited physical impostors to go into the branches and pose as the real customers.
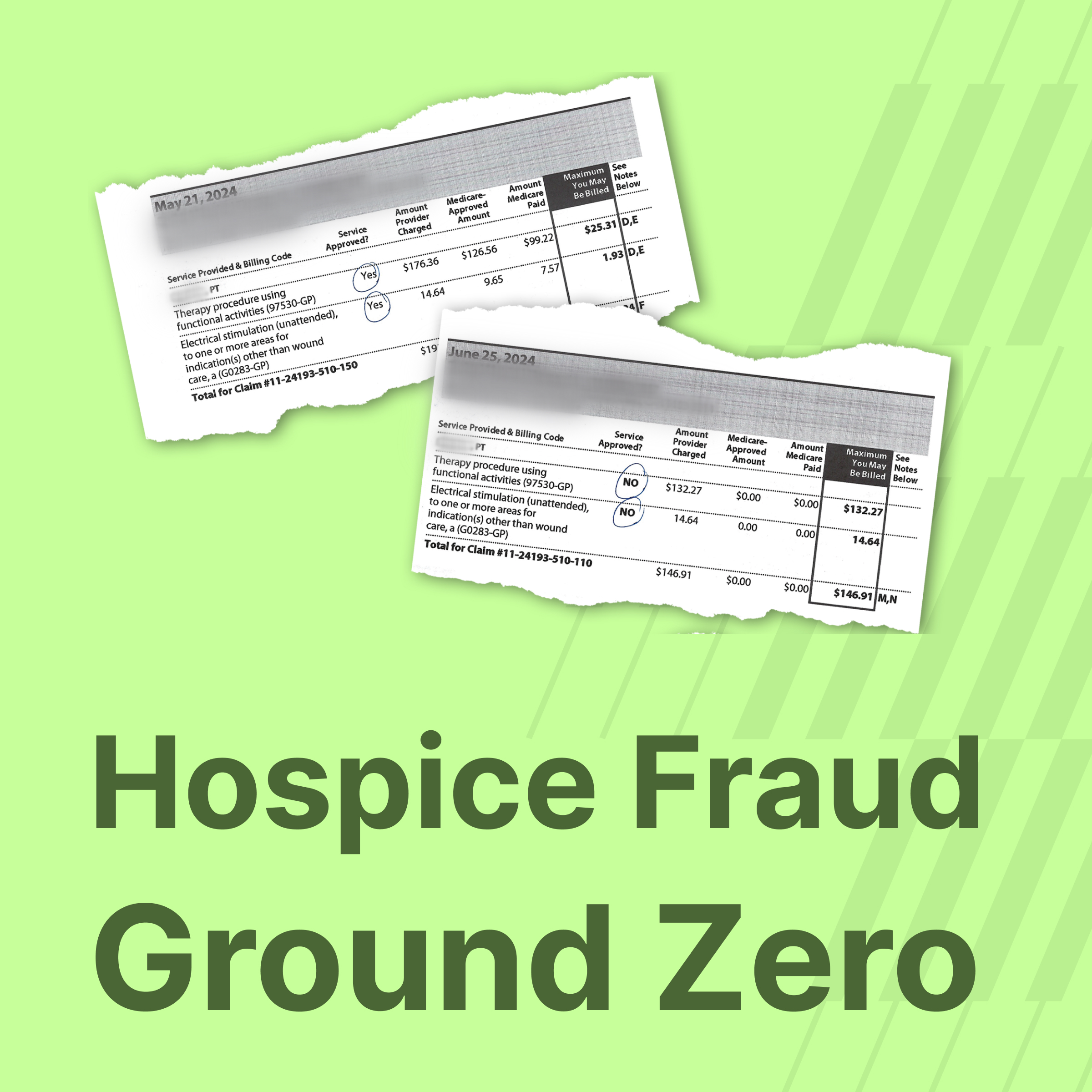
The impostors carried fake IDs that bore the real customers' identifying information alongside the impostors' photos. At the teller window, those fraudulent documents were enough. Large sums were withdrawn as cashier's checks, which Kolawole and Wainaina then deposited into accounts they controlled. From there, the proceeds flowed back to Vernot, who used the funds to pay the impostors and the bank employees who had intentionally skipped customer verification procedures to let the transactions through.
By the time federal prosecutors pieced it together, Wainaina had deposited or attempted to deposit more than $762,000 in fraudulently obtained cashier's checks. Kolawole had deposited approximately $373,000. The total exposure across all six co-conspirators has not been fully detailed in public filings, but the guilty pleas confirm a multi-million dollar operation.
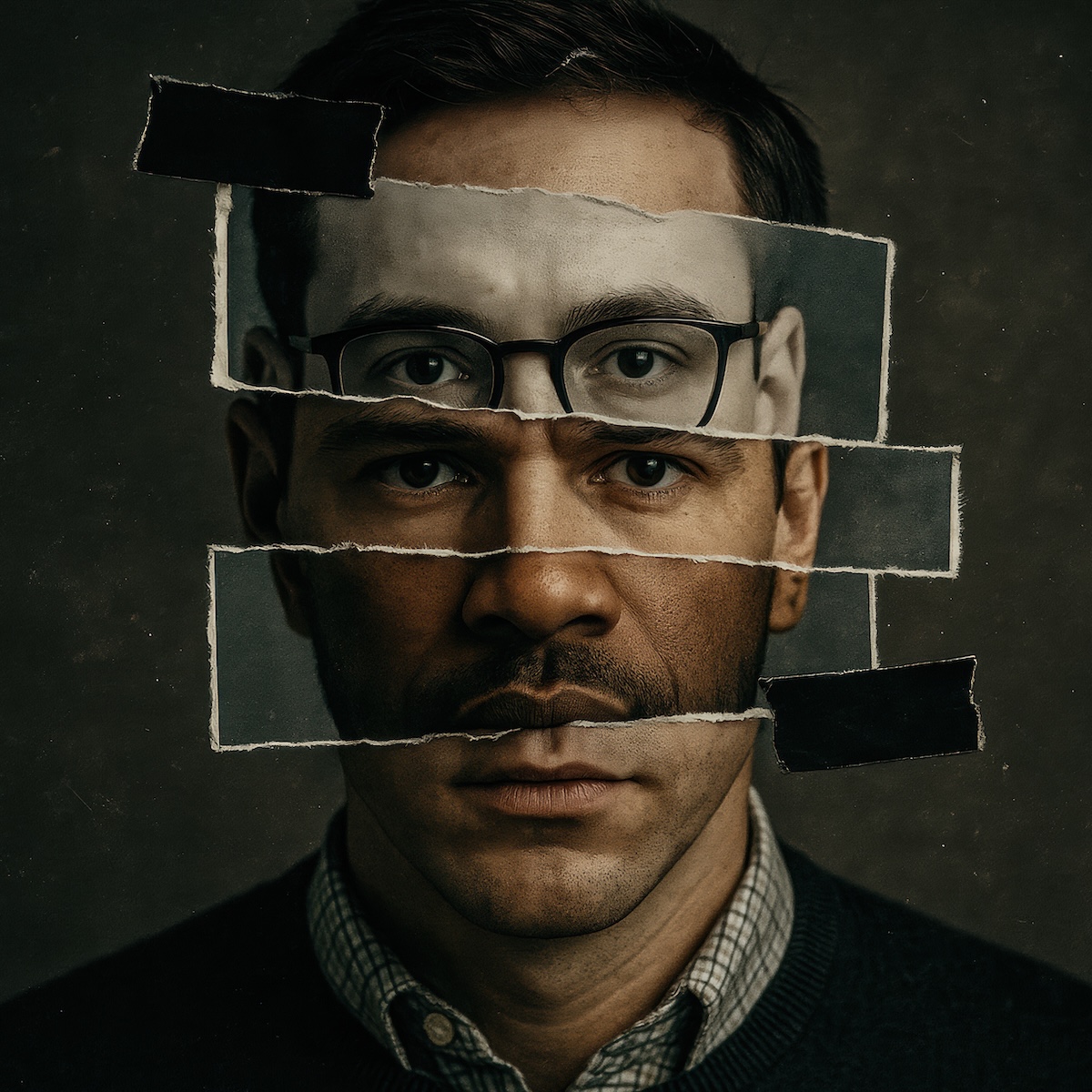
The first failure: A fake ID that passed the teller's eye test
The foundation of this scheme was the forged identity document. Real customer PII on a fake card carrying the impersonator's photo. At the teller window, a bank employee had to make a visual judgment call about whether the person in front of them matched the information on the ID. That judgment call failed, repeatedly, across multiple branches and multiple states.
This is one of the most documented weaknesses in branch-based identity verification. Most bank tellers are not trained document examiners. They are not equipped to detect signs of a doctored driver's license, and they are being asked to make high-stakes fraud determinations under the time pressure of a normal transaction. The result is a verification standard built on a guess.
Check fraud-related Suspicious Activity Reports filed with FinCEN reached an estimated 682,276 in 2024, representing an increase of roughly 95% since 2020. The method behind much of that fraud is the same method this ring relied on: exploiting the moment of human review. Physical impersonation with doctored documents remains effective precisely because visual inspection is not a reliable control.
For fraud and risk teams at financial institutions, this case is a clear illustration of why teller-based ID review has to be augmented with technology that can actually interrogate the document.
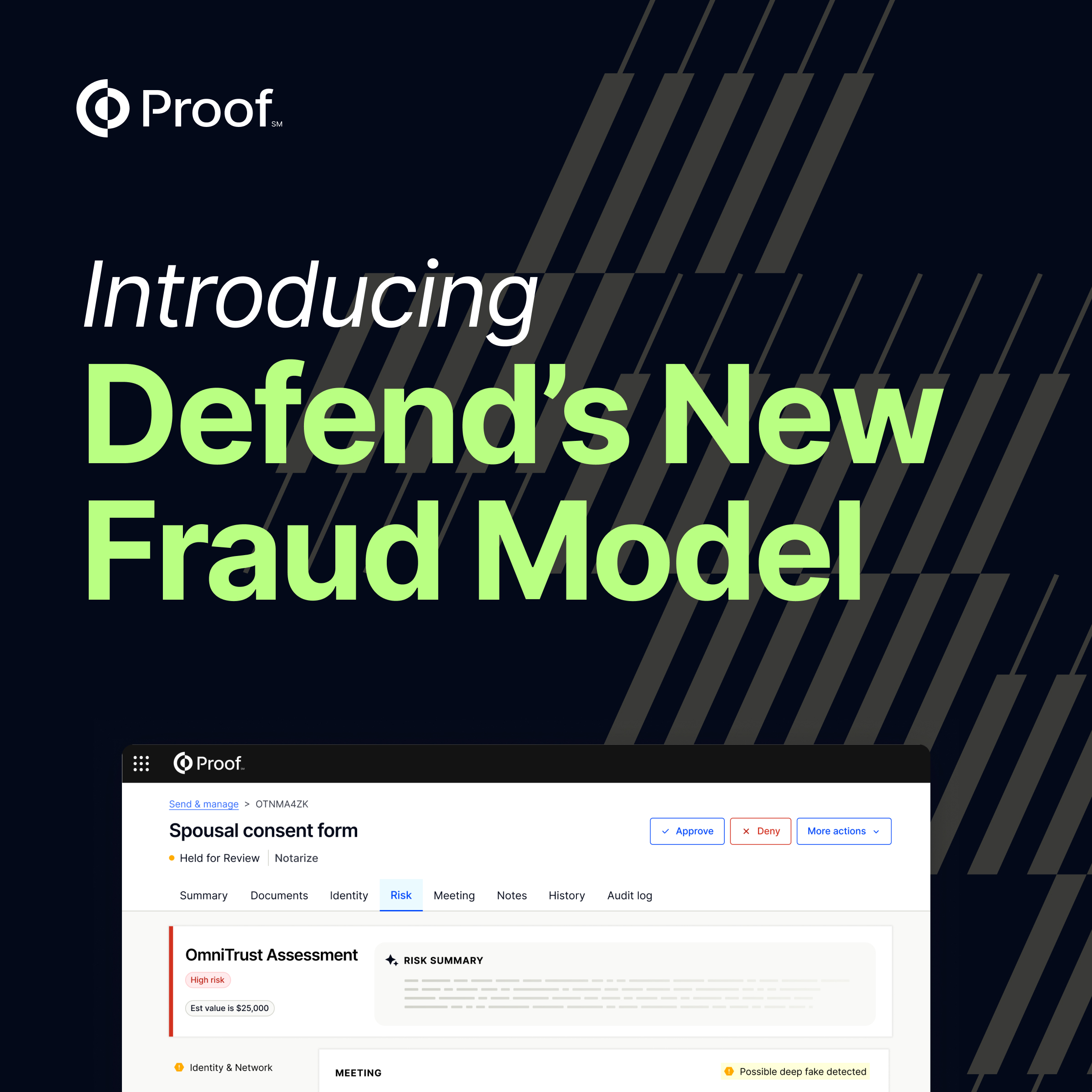
Proof was built for exactly this gap. When a customer initiates an identity verification through Proof, they are required to submit a government-issued ID and a real-time biometric selfie. The platform performs automated document analysis to detect signs of tampering or forgery. It verifies U.S. driver's licenses directly against DMV records through AAMVA integration, confirming that the document matches a real identity on file and flagging discrepancies the moment they appear. A biometric face match then compares the submitted selfie against the photo on the ID, with liveness detection confirming the person is physically present, not submitting a static image or a deepfake.
A doctored ID carrying the wrong face does not pass those checks. The impostors in this scheme would have been flagged before the transaction ever reached a teller.
The second failure: Employees bypassed the controls that existed to catch it
If the fake ID was the first line that failed, the bank insiders were the second.
According to federal prosecutors, bank employees intentionally skipped customer verification procedures to facilitate the withdrawals. These were people already inside the institution, with account access and the authority to override the controls designed to protect customers. Their participation transformed a scheme that might have been stopped at the teller window into one that ran for years.
Insider-enabled fraud at financial institutions is not a fringe problem. The ABA Banking Journal recently highlighted growing concern about insider threat risk across banking, noting that the financial sector is among the most frequently targeted industries for this type of attack. The Massachusetts case fits a pattern that compliance and KYC teams know well: where identity verification relies on employee discretion, corrupt or pressured employees become the vulnerability.
Most branch-based verification processes are ultimately discretionary. They depend on an employee's willingness to follow a checklist, and when the employee is the one who has been compromised, no checklist helps.
Proof removes that single point of failure.
Proof routes high-risk and high-value transactions through a structured, technology-enforced verification workflow. A live Trusted Referee conducts a face-to-face video verification with the customer and reviews the submitted identity documents in a secure, audited environment. The process cannot be abbreviated, skipped, or overridden at the branch level. Every step is recorded, and every verification event generates a tamper-evident digital record that documents what was checked, by whom, and when.
For compliance and KYC teams, this shifts the nature of the verification record entirely. Proof creates an auditable, evidence-backed record: here is proof that the verification happened, or here is proof that it did not. When fraud surfaces and regulators start asking, that distinction carries real weight.
Two vulnerabilities. One platform that addresses both.
The Massachusetts fraud ring succeeded because it found two soft spots in the same institution: the document review moment, and the employee who was supposed to catch what document review missed. That combination is not unique to this case. Fraud rings specifically look for the gap between controls, where one weak point compounds another and the scheme moves faster than any single human can track.
Proof is built to close both gaps. Our identity verification technology replaces visual document inspection with automated forensic analysis, real-time DMV verification, biometric confirmation, and liveness detection. And our workflow enforcement removes human discretion from the verification event entirely, replacing it with a structured, recorded process that creates durable evidence whether the transaction is legitimate or not.
Banks operating with teller-based document review and employee-enforced verification are running with the same two gaps this ring exploited for two years.
Schedule a demo with our team before the next fraud ring finds yours >

























.jpg)

























































.png)

.jpg)