Passwordless Security: Why the Future of Authentication Still Starts with Identity

For years, logging into an account has followed the same basic pattern:
- Enter a username
- Enter a password
- Add a second factor (i.e. a code or push notification)
That model has improved over time, but it still relies on a fragile assumption. A password is treated as proof that the person logging in is who they claim to be.
Attackers understand that assumption just as well as defenders do. Phishing attacks capture credentials. Password reuse exposes accounts after breaches. Even multi-factor authentication can be bypassed when attackers convince someone to approve a login request or reset access.
Because of these weaknesses, many organizations are moving toward passwordless authentication.
Instead of relying on passwords, these systems use stronger signals such as passkeys, biometrics, or hardware security keys. Authentication becomes tied to devices and cryptographic keys rather than shared secrets that can be stolen or reused.
For security teams and product teams alike, the appeal is straightforward. Passwordless systems reduce the risk of credential theft while also making login faster and easier for legitimate users.
But removing passwords does not eliminate identity risk. It simply changes where that risk appears.
Why passwordless adoption Is accelerating
Passwords remain one of the most common sources of both security incidents and operational friction. Users forget them, reuse them across services, and store them in ways that make them easy targets for attackers.
Passwordless authentication addresses many of these problems directly. Instead of entering a secret that can be copied or reused, users authenticate with device-bound credentials such as passkeys or hardware security keys.
Adoption has accelerated quickly as major technology platforms have expanded support for passkeys across browsers, devices, and operating systems.
Research from the FIDO Alliance shows that passkey sign-ins succeed about 93% of the time, compared with roughly 63% for traditional authentication methods, while the average passkey login takes about 8.5 seconds compared with more than 30 seconds for many password-based MFA flows.
These improvements explain why many organizations see passwordless authentication as both a security upgrade and a usability improvement.
Yet authentication is only one part of the access lifecycle. Even in passwordless systems, users still lose devices, replace phones, enroll new credentials, or request help restoring access.
Those moments are where identity risk often reappears.
Where passwordless systems still struggle
Security teams often focus on the login experience when deploying passwordless authentication. That is the moment where passwords disappear and new authentication methods take their place.
Attackers, however, rarely attack the strongest part of a system. Instead, they look for the processes designed to help legitimate users regain access.
Even in passwordless environments, those processes still exist. Someone replaces a phone and needs to enroll a new passkey. An employee loses access to a hardware key. A customer contacts support asking for help restoring their account.
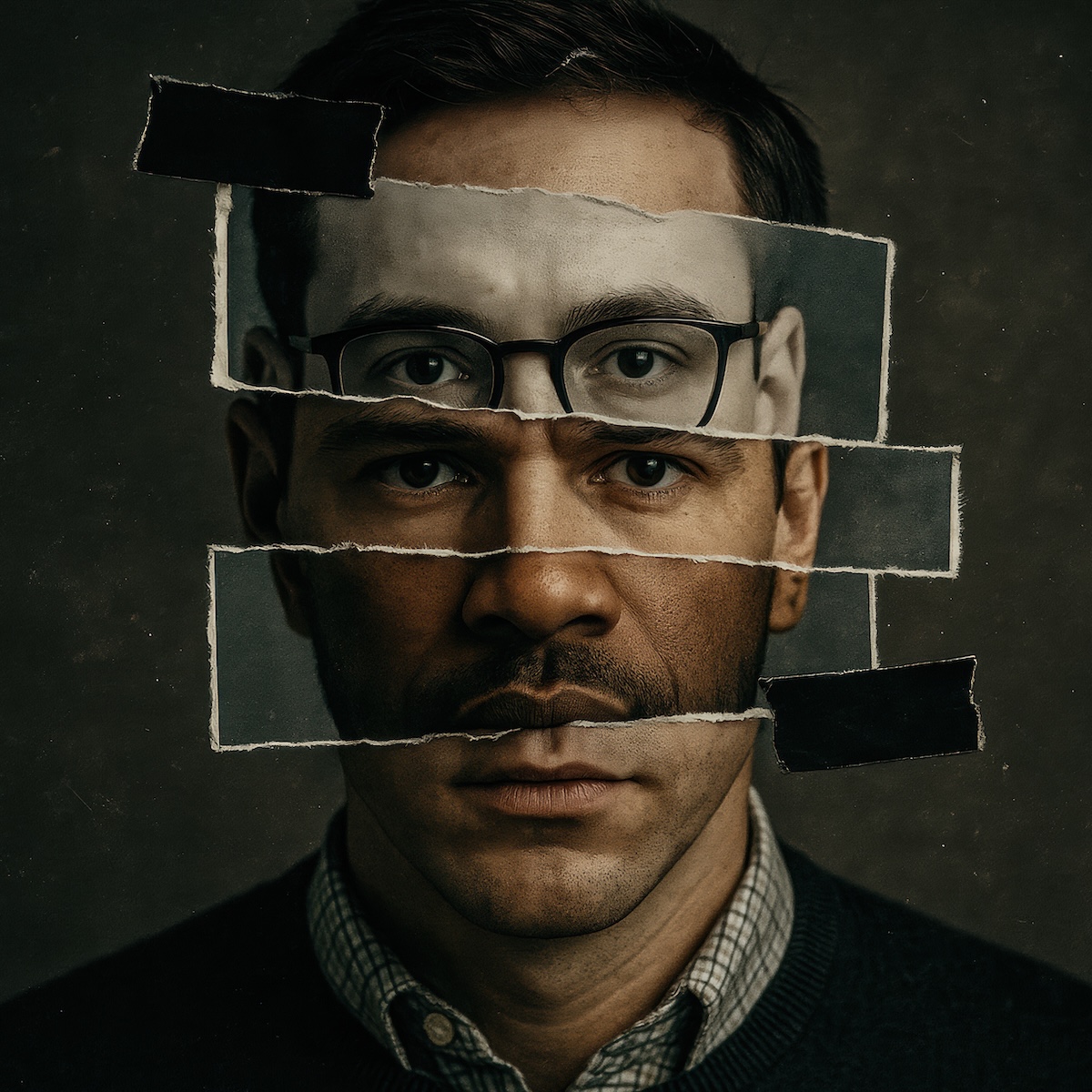
If identity is not verified during those moments, attackers can still gain access by impersonating legitimate users.
In practice, many of these decisions fall to help desk teams or automated recovery workflows. Someone requests access, a code is sent, and the account is restored. But if the attacker already controls the victim’s email or device, that process confirms possession but not identity.
Passwordless systems remove passwords, but they do not remove the need to confirm who someone actually is.
Why identity becomes the critical layer
Authentication and identity are often treated as the same concept, but they answer different questions.
Authentication confirms that a device has the correct credentials.
Identity verification confirms that the person requesting access is actually who they claim to be.
In password-based systems those ideas often overlap. Entering the correct password is treated as proof of identity. Passwordless systems separate them.
Devices can authenticate quickly through passkeys or hardware keys, but organizations still need a reliable way to confirm identity when access changes. That includes moments such as account recovery, device enrollment, replacing authentication methods, or restoring locked accounts.
These events happen frequently. Estimates often cited by Gartner suggest that 20 to 50 percent of IT help desk calls relate to password resets, highlighting how often access recovery becomes part of day-to-day operations.
As authentication becomes easier, identity verification becomes more important. Organizations that succeed with passwordless security design their workflows around that shift.
Where identity verification fits
To close this gap, many organizations introduce identity verification during high-risk access changes.
Instead of relying on security questions or email access during recovery, they verify the person requesting access directly. This may include verifying a government ID, performing biometric matching with liveness detection, or recording a verification session that confirms identity.
These approaches allow organizations to restore access or enroll new credentials without relying on signals attackers can easily compromise.
They also provide something security teams often lack when investigating account takeover incidents: a clear record of who requested access and how identity was confirmed. That evidence changes how organizations approach access security.
Passwordless security still starts with identity
Passwordless authentication represents a significant improvement for both security and usability. It reduces reliance on passwords, limits the effectiveness of phishing attacks, and simplifies login experiences.
But removing passwords does not eliminate identity risk - it simply moves the most important security decision to a different moment in the workflow. When someone asks for access.
Organizations that succeed with passwordless security recognize that authentication and identity verification must work together.
Authentication confirms the device.
Identity verification confirms the person.
Together, they create a stronger foundation for secure digital access.
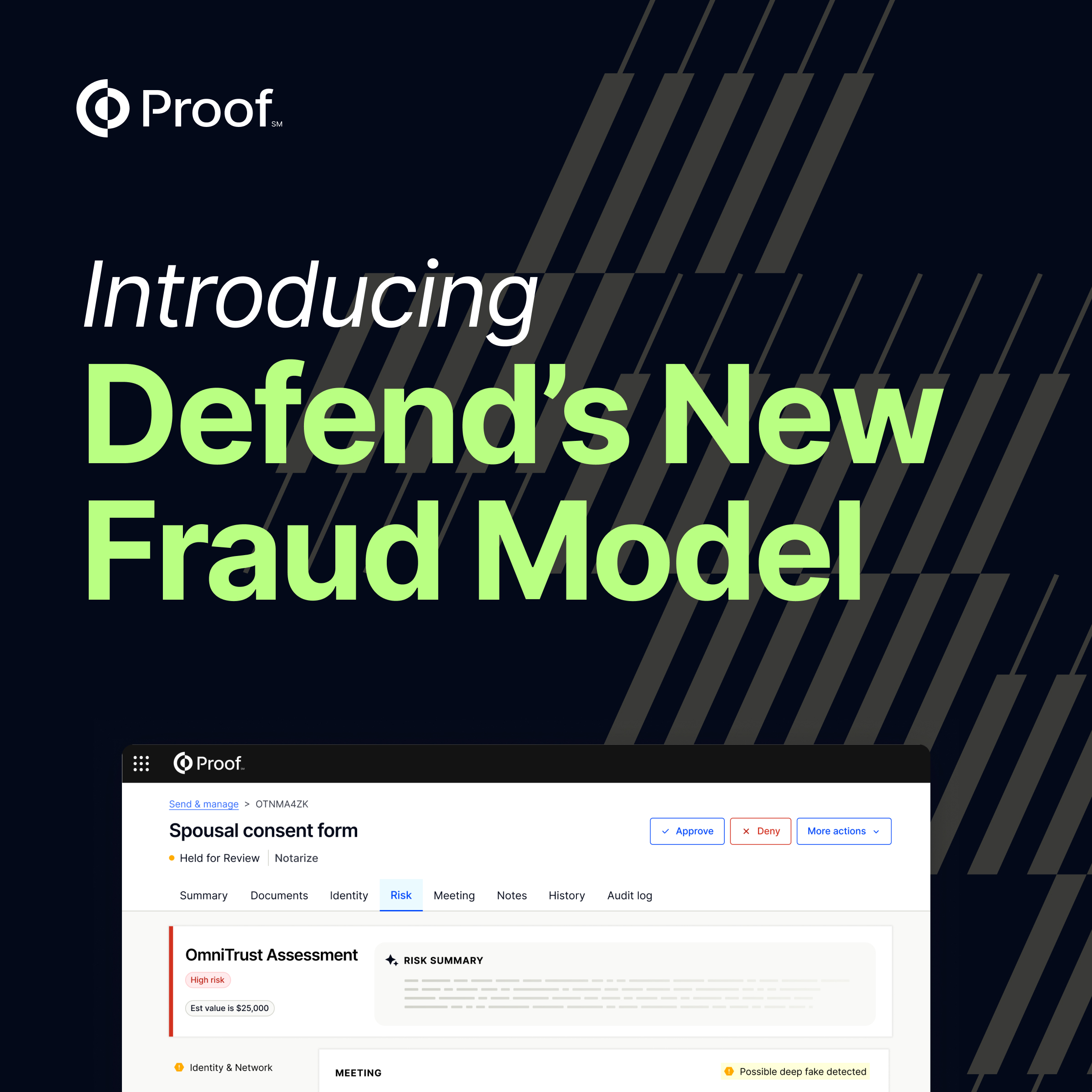
Proof helps organizations strengthen passwordless authentication by verifying the identity of users before critical access changes happen. That includes moments such as account recovery, device enrollment, and credential replacement.
By confirming identity at these points, organizations can support passwordless login experiences while reducing the risk of impersonation and account takeover.
Explore how organizations are securing account recovery with Proof >



























.jpg)























































.png)

.jpg)