Why KYC Alone No Longer Stops Fraud (and What Comes Next)

Know Your Customer (KYC) requirements exist for one reason: regulatory compliance. They were created to help governments prevent specific crimes like money laundering, terrorist financing, and sanctions evasion by requiring businesses to collect and verify customer information at onboarding.
KYC was never designed to help businesses actually know who is behind an account over time.
That distinction matters more than ever.
Today’s fraud doesn’t fail KYC. It passes it. Synthetic identities built from real data, credential reuse across platforms, and AI-generated documents routinely clear onboarding checks without triggering alarms. When fraud happens weeks or months later, it’s not because KYC was skipped. It’s because KYC already did everything it was designed to do.
Fraud teams across banking, fintech, marketplaces, and payments are seeing the same pattern: accounts that pass KYC cleanly and then commit fraud downstream. The problem isn’t execution. It’s expectation. KYC is a regulatory control. Modern fraud is an identity problem.
To stop it, organizations need a better answer to a harder question: How do you actually know your customer is the one taking this action right now?
That’s where KYC ends, and what comes next begins.
Why KYC is no longer sufficient to prevent fraud
KYC verifies whether customer information matches trusted data sources at onboarding. It confirms that a name, date of birth, or identification number aligns with existing records to meet compliance requirements.
Modern fraud does not try to break that model. It works within it.
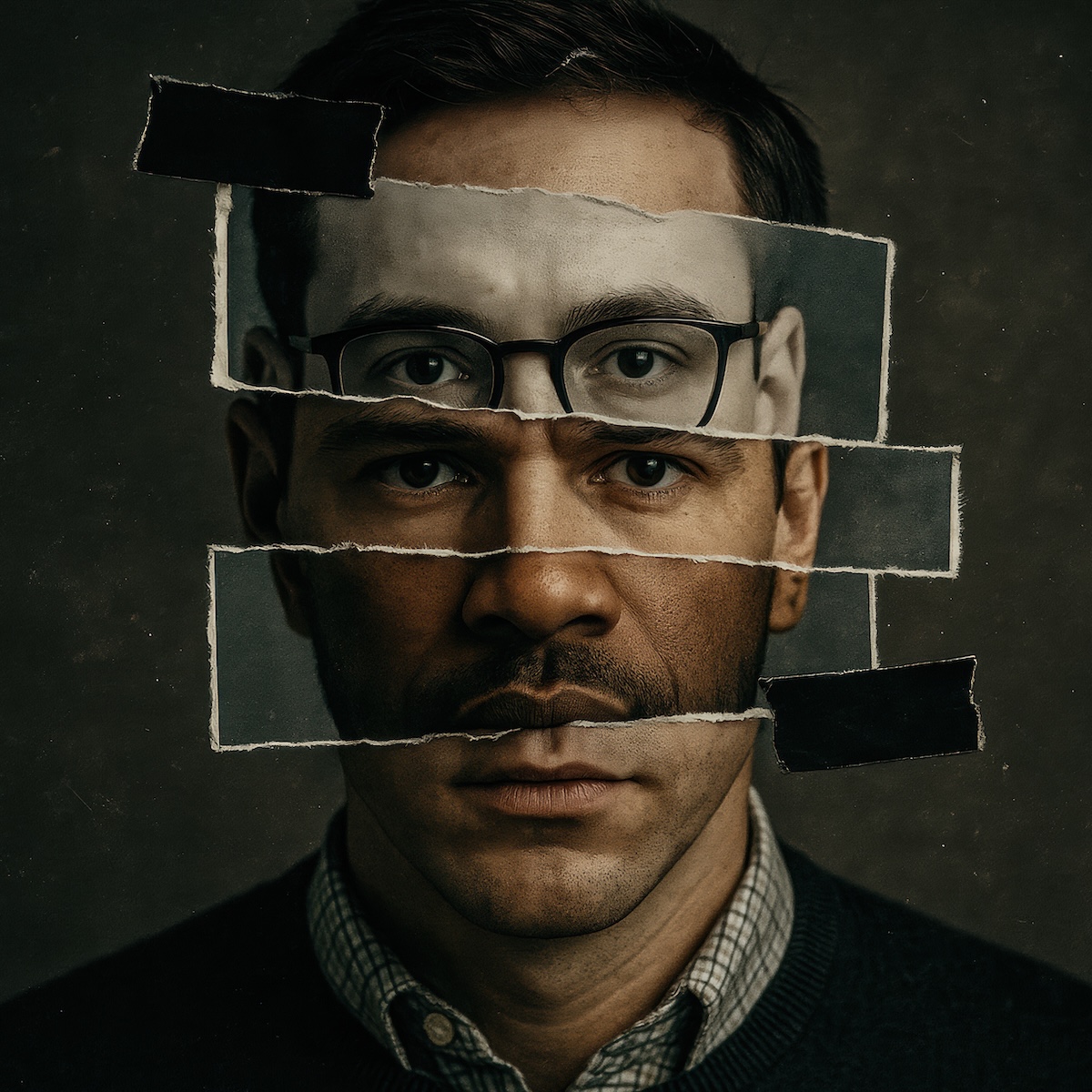
Synthetic identities are assembled from real data. Stolen credentials are reused across institutions. AI tools generate convincing documents that clear automated checks. Passing KYC often means the fraudster obtained accurate information, not that a legitimate person is present.
Organizations with mature KYC programs still see account takeovers, fraudulent payouts, and downstream abuse. Not because KYC failed, but because KYC validates data at onboarding. Fraud exploits identity and authorization over time.
The limitations of KYC in a modern fraud environment
KYC programs were built to satisfy onboarding compliance obligations, not to maintain identity assurance across the customer lifecycle. That creates natural coverage gaps as risk evolves.
- First, KYC is static. Once onboarding checks are complete, most systems assume the approved identity remains in control.
- Second, KYC lacks continuity. High-risk actions that occur weeks or months later are rarely tied back to the originally verified individual.
- Third, KYC produces limited evidence. When fraud occurs, teams often cannot prove who authorized a change or whether the legitimate user was present at the moment of approval.
These gaps appear most often during high-impact events like account recovery, payment changes, refunds, and payouts. Moments where authorization matters more than onboarding data.
Why fraud happens after KYC, not during it
Many fraud strategies are intentionally designed to clear onboarding controls.
Accounts may behave normally for extended periods to build trust. Fraudsters wait until balances grow, limits increase, or recovery pathways open. Risk emerges during account use, not at account creation.
This timing is not accidental. KYC concentrates scrutiny at onboarding because that is where regulatory risk is highest. Fraud concentrates activity later because that is where financial opportunity is greatest.
Treating KYC as a full lifecycle fraud control leaves organizations exposed precisely where authorization matters most.
KYC vs. identity verification - what’s the difference?
KYC and identity verification are often used interchangeably, but they answer different questions.
KYC asks: Does this customer meet regulatory onboarding requirements?
Identity verification asks: Is a real person present, in control, and authorized to take this action?
High-assurance identity verification relies on signals that are harder to steal or fabricate. Live biometrics, document authenticity analysis, device intelligence, and human review when automation falls short.
It produces audit-ready evidence tied to an individual, not just a pass or fail result tied to submitted data.
This distinction becomes critical when trust must extend beyond onboarding into ongoing account activity.
What comes after KYC: digital identity
To close these coverage gaps, organizations are moving toward persistent digital identity.
Digital identity treats verification as an ongoing capability rather than a one-time event. A verified identity can be reused, revalidated, and strengthened as risk changes over time.
Instead of assuming trust persists, systems can step up verification during sensitive moments like credential resets, payout approvals, or account changes. Each high-risk action is tied back to a verified individual with clear evidence of when and how identity was confirmed.
This approach reduces fraud exposure without introducing unnecessary friction for legitimate users. Verification happens when risk demands it, not every time a customer logs in.
Where KYC still fits in a modern identity strategy
KYC remains an essential baseline. Regulatory requirements still apply, and onboarding screening is necessary. But KYC is most effective when paired with high-assurance identity verification and persistence across the lifecycle.
Together, they allow organizations to answer a more operationally meaningful question than “Did this pass KYC?” They allow teams to ask: Can we stand behind who authorized this action?
That shift matters for fraud prevention, compliance defensibility, and customer trust.
AI-driven fraud, scalable synthetic identities, and credential reuse have reshaped the risk landscape. The tools fraudsters use evolve faster than static identity programs can adapt. Passing KYC no longer guarantees legitimacy. In many cases, it only confirms that accurate data was used at onboarding.
Organizations that rely on KYC alone will continue to see losses emerge downstream. Those that adopt digital identity models are better positioned to detect risk, verify authorization, and create evidence across the full customer journey.
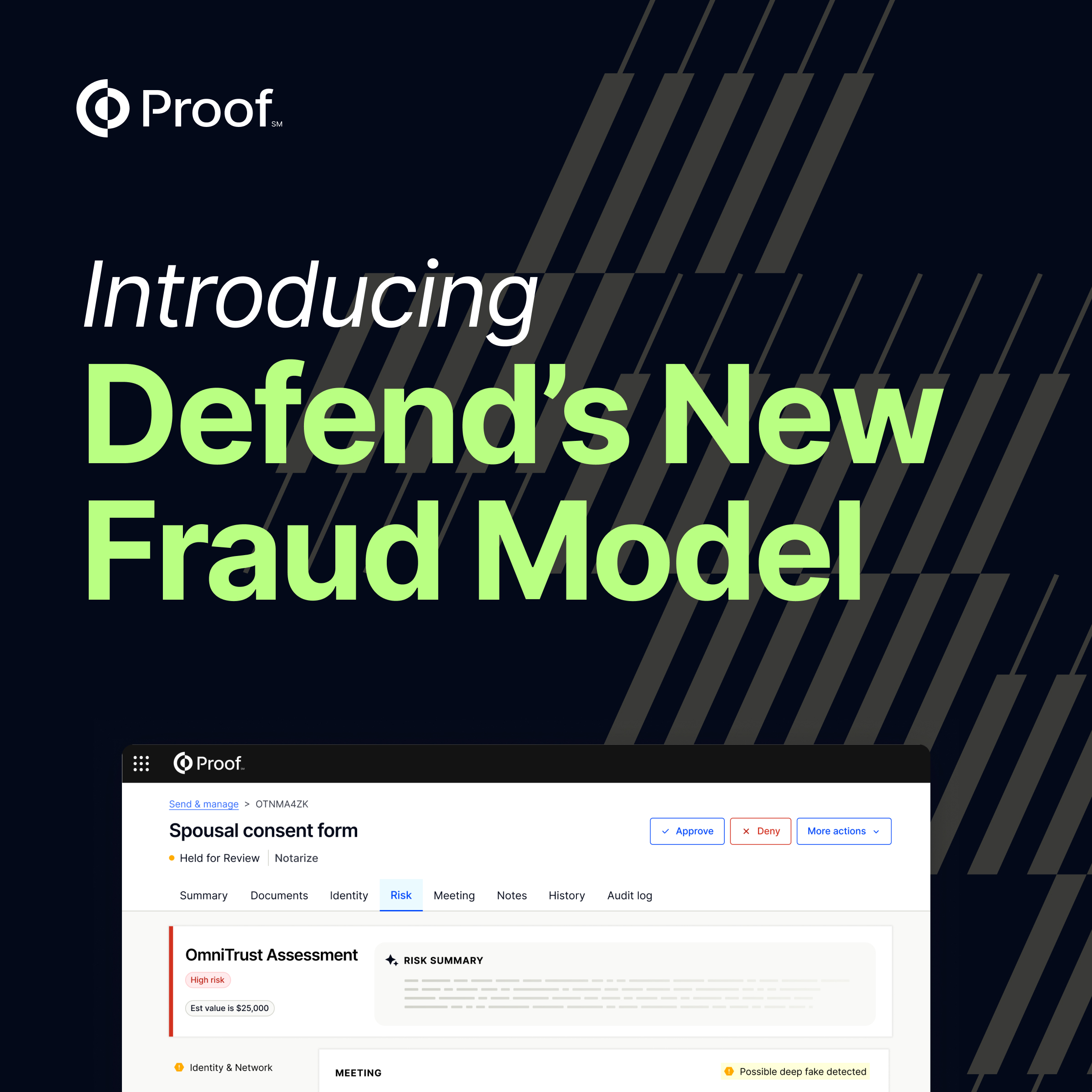
Proof helps organizations move beyond one-time onboarding checks by establishing persistent digital identities that can be verified, reverified, and trusted over time.
With high-assurance identity verification, reusable identity records, and step-up workflows designed for high-risk moments, Proof enables teams to tie actions to real people and create evidence they can stand behind.




















.jpg)






































































.png)

.jpg)