Proof your hiring process.
Prevent candidate fraud from application to day one.
Stop deepfake candidates, proxy interviews, and identity fraud from application to day one.
Most hiring tools verify once and move on. Proof builds a continuous identity record across every stage of your funnel, reinforced by trained human experts at the moments that matter most.
Spotting Fake Applicants in Hiring
What HR teams need to know about deepfake interviews, synthetic identities, and the fraud that background checks miss.
Fraud has industrialized.
Your hiring stack hasn't caught up.
1 in 4
job applicants will be fake by 2028
of recruiter time wasted per job posting on fraudulent candidates
cost exposure from a single nation-state actor hired as an IT engineer
.png)
AI didn't create hiring fraud. It made it available to everyone.
What once took nation-state resources now takes a $20 tool and 20 minutes. Synthetic identities, AI-generated documents, deepfake video — the attack surface is expanding faster than any single checkpoint can track.

Your hiring stack was built for a different threat.
Current tools only offer fragments. Background checks verify history, scanners hunt AI text, and risk signals block bots. Even ID checks provide just a static snapshot. Each solves a piece of the puzzle, but none hold the thread from start to finish.

This problem will not age out. It will accelerate.
Deepfakes are getting cheaper. Synthetic identities are getting more convincing. The same AI driving your recruiting automation is driving your fraud exposure. A point solution that works against today's attacks may be obsolete before your next hiring cycle.
The problem demands more than a point solution.
So we built one.
Proof is the only platform that combines a persistent identity record, trained human experts at every critical stage, and a network built to evolve as fraud does, so you're not back in six months looking for something else.

Specialized identity agents, not recruiter guesswork
Proof identity agents step in at high-stakes moments, removing the burden of verification from your recruiters, so they can focus on talent - while we ensure candidates are who they say they are.

I-9 as a fraud signal, not just a compliance box
Proof's remote I-9 examination is a fraud detection moment. A fraudulent hire cannot match the identity they rode in on. The I-9 surfaces what algorithms miss entirely.

A continuous identity thread, not isolated checkpoints
Proof builds an unbroken chain from application to Day One. If the thread breaks anywhere, you know before they start.
Not a checkpoint.
A continuous identity thread.
Proof doesn't verify once and move on. Each stage builds on the last so trust compounds, the identity record strengthens. If something breaks anywhere in the thread, you know before it becomes a problem.
Passive fraud screening at intake
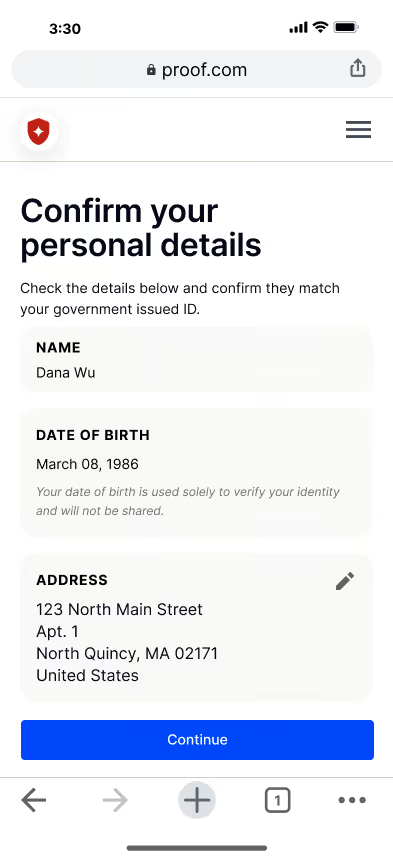
The moment a candidate enters your pipeline, Proof automatically evaluates their application data — name, email, phone, address — against a set of risk signals that surface synthetic identity patterns, high-risk contact data, and behavioral anomalies. A risk score writes back directly to your ATS. Recruiters see it in context, filter on it, and act on it without ever leaving their workflow. Zero candidate friction. Zero workflow changes. The identity record starts here.
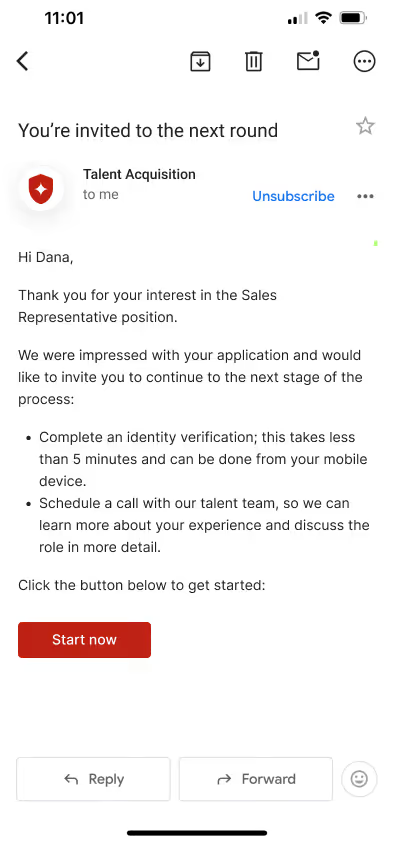
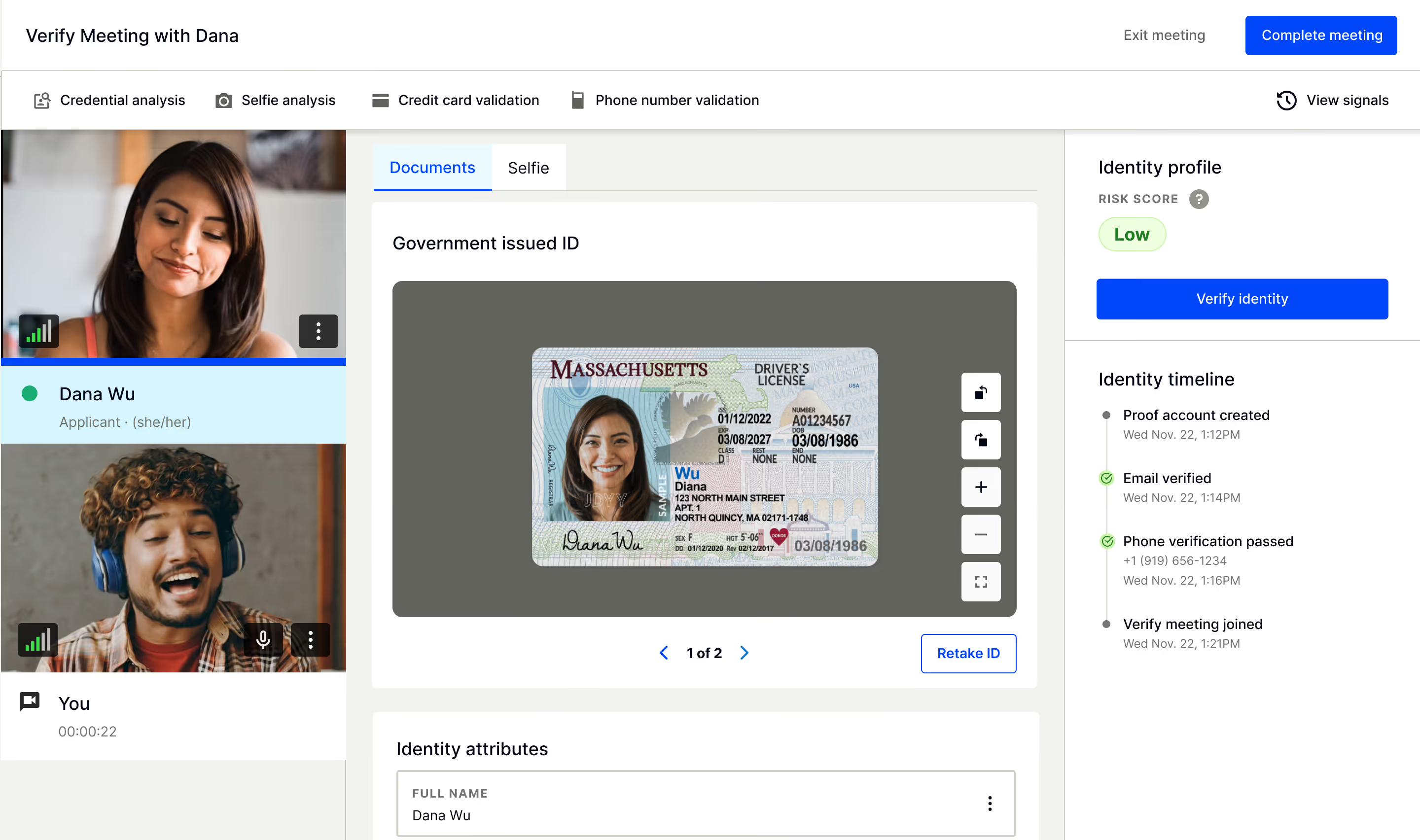
Automated identity verification
When a candidate reaches the shortlist, Proof triggers identity verification — no manual steps, no candidate portal to explain. Government ID and liveness checks confirm the person is real and matches who applied. Results write back to your ATS natively, so your recruiters stay in their workflow. The verification depth is configurable by role, team, or risk level — because not every role carries the same exposure. This is where the identity record deepens.
Identity continuity through every round
Your recruiters and interviewers make the calls. Proof makes sure they're making them with the right information. As candidates move through the interview loop, their verified identity travels with them — a consistent, established record your team can reference at any stage. For high-stakes roles, Proof can re-check the person in the room against the identity on file. Not a new verification from scratch. A check against someone you already know.
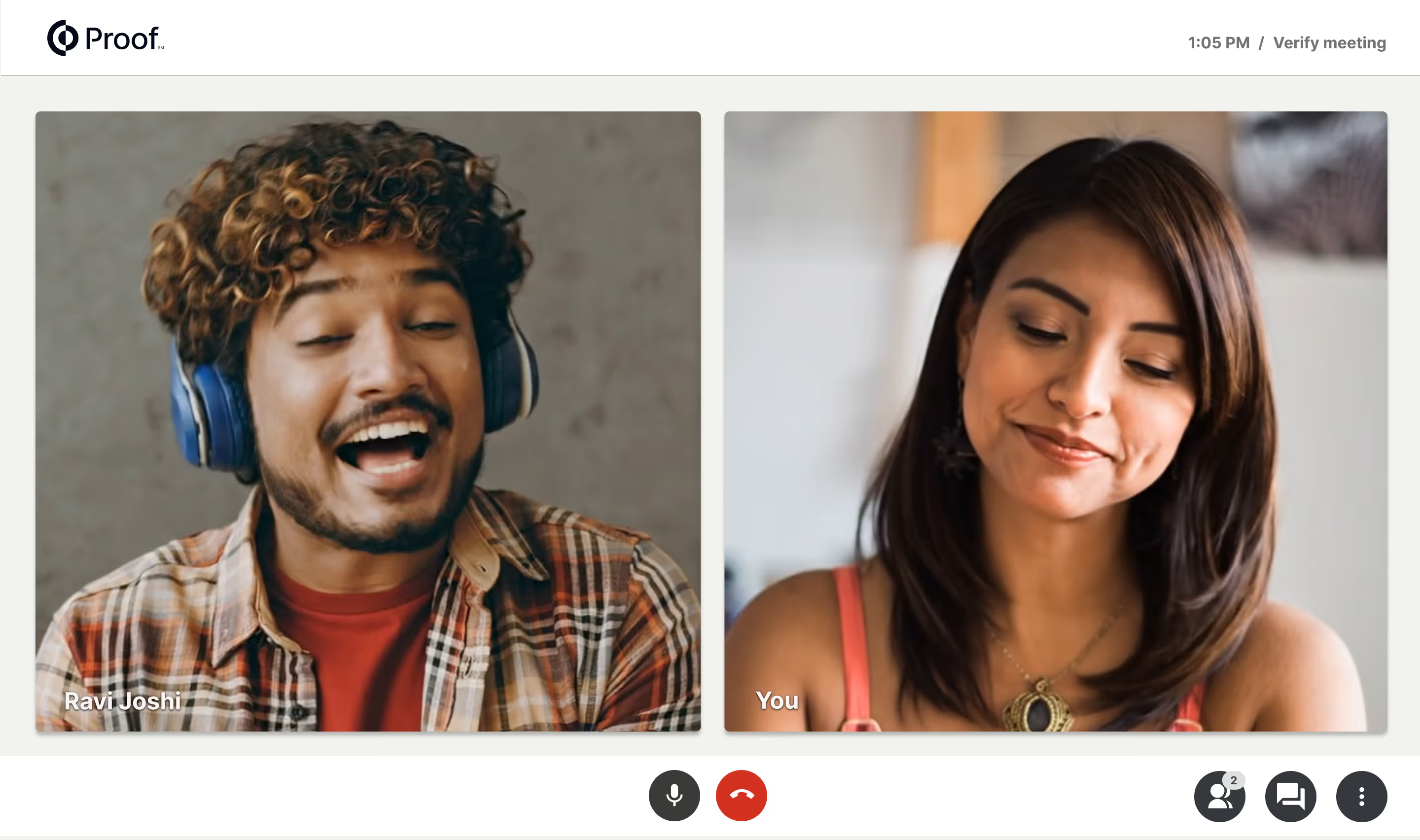
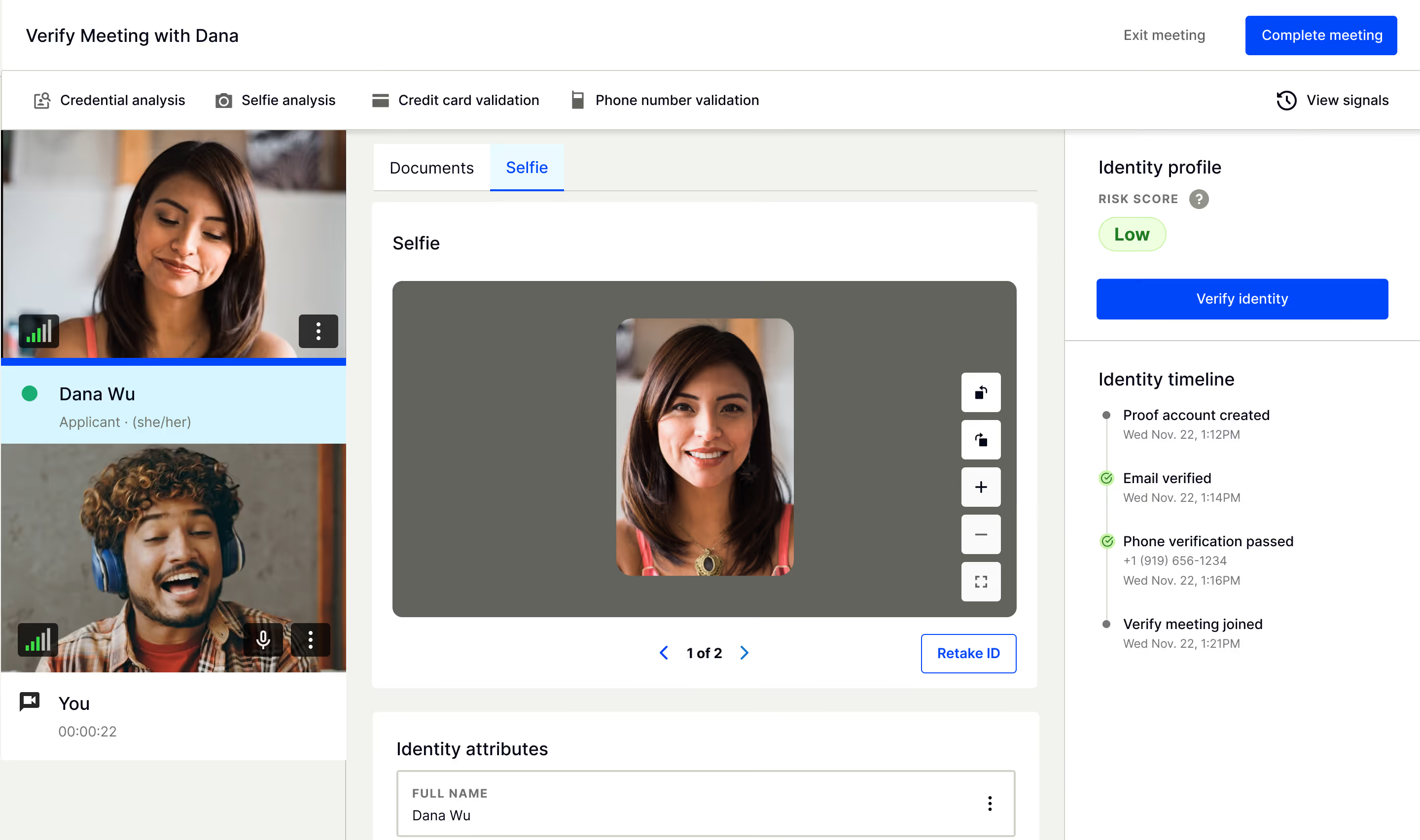
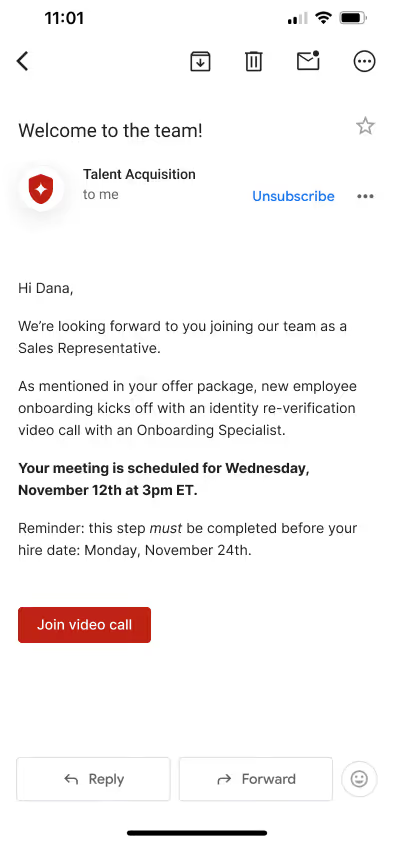
Live human verification before the offer is signed
Before an offer is signed, have an authorized representative or Proof identity agent join the session. Regardless, they arrive with full context: risk signals, prior verifications, the complete identity record built across every stage. Deepfake detection runs in real time. New risk signals from the session are layered against everything already known about this person. If something doesn't add up — a hesitation, a document inconsistency, a face that doesn't match — a human catches it. For executives, engineers with system access, and roles with elevated exposure, this is your last informed gate before someone walks in the door.
I-9 as compliance proof and final fraud catch
By Day One, you already know who the applicant is. Proof's remote I-9 closes the record that started at application. Live document review, a face check against the verified identity on file, and the complete audit trail returned automatically.
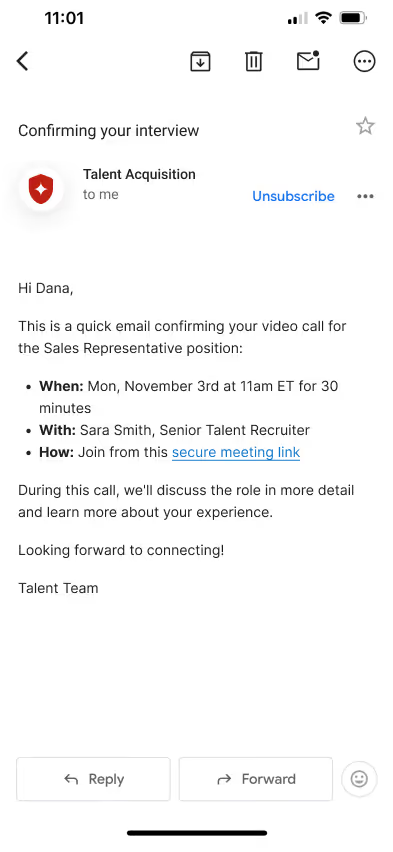
The verified candidate experience
From the first email to Day One — What your candidate sees, and what your hiring team experiences behind the scenes.
Hiring teams trust Proof.
Works with the hiring stack
you already use.
Proof connects to your ATS, HRIS, and background check tools — no rip and replace. Verified results write back automatically.


Candidate fraud
won't slow down.
Neither should you.
Talk to us about how Proof can help your HR team catch fakes early — and stay focused on what matters most: hiring the best people.
- Live human identity verification — not just algorithms
- Deployable in hours — no engineering required
- Integrates with your ATS, HRIS, and HRMS
We've heard every objection.
We already do background checks. Why do we need this?
Background checks verify what a candidate claims about their past. They don't verify who the person is in front of you — and by the time they run, a fraudulent candidate has already passed 3–5 interview rounds, wasted thousands in recruiter hours, and potentially accessed your systems. Proof catches fraud at the top of the funnel, before any of that happens.
Will this slow down our hiring process?
Proof's Defend product runs passively in the background — candidates don't know it's happening and don't need to do anything. The only friction is for fraudsters. Legitimate candidates move through your pipeline faster because recruiters aren't wasting time on fake applications. Passive screening plus triggered IDV means you run full verification only on candidates who need it.
What about candidate experience and drop-off?
Up to 25% of applications for certain roles are already bots or fake candidates. Proof's passive-first approach means legitimate candidates experience zero friction unless a risk signal warrants step-up verification. A candidate who refuses to verify their identity is telling you something important — that's not a drop-off problem, it's a data point.
We have data privacy and legal concerns.
Proof is an identity validator, not a decision-maker. We don't make hiring decisions — we verify identity. Our platform includes EEOC/CRA-compliant posture, proactive data handling documentation for procurement review, and legal sign-off pathways. We're deployed at healthcare companies, insurance carriers, and financial institutions with the strictest regulatory environments in the country.
What's the ROI if we don't catch many fraudsters?
Measure beyond fraud catches. Recruiter efficiency alone: 42 hours saved per job posting × your number of open roles = thousands of hours recovered annually. Then factor in average cost of identity fraud at $500K–$1M+ per incident, $1M–$5M+ for a malicious insider, $5M–$50M+ for a nation-state actor. Proof is the insurance policy — you don't measure fire insurance by how many fires you've had.
How long does implementation take?
Proof deploys in hours with no-code EasyLinks and ATS webhooks. No engineering required to get started. Building a comparable in-house solution would take 12–18 months and millions in spend — and you still wouldn't have the fraud signal network built from millions of verified users and billions of transactions. That scale is the moat you can't replicate.
The Candidate Fraud Survival Guide
What HR and talent teams need to know about deepfake interviews, synthetic identities, and the fraud background checks miss.