The $17 Million Infiltration: How Modern Fraudsters Exploit the Mechanics of Real Estate


A federal mortgage fraud case in Los Angeles is ringing alarm bells across the title and settlement industry.
The U.S. Department of Justice charged 11 people in a sophisticated conspiracy targeting elderly homeowners. By stealing identities, these criminals secured millions in hard money loans against properties they had absolutely zero claim to.
For title agents, the takeaway is clear. Fraudsters are stepping out of the digital shadows and inserting themselves directly into the transaction as seemingly legitimate players.
Anatomy of the scheme: How they pulled it off
These bad actors bypassed software firewalls to hack the human mechanics of the real estate process itself. Their operation followed a clinical manual:
- Targeting the vulnerable: The group zeroed in on older homeowners with high equity and a low likelihood of checking their property records.
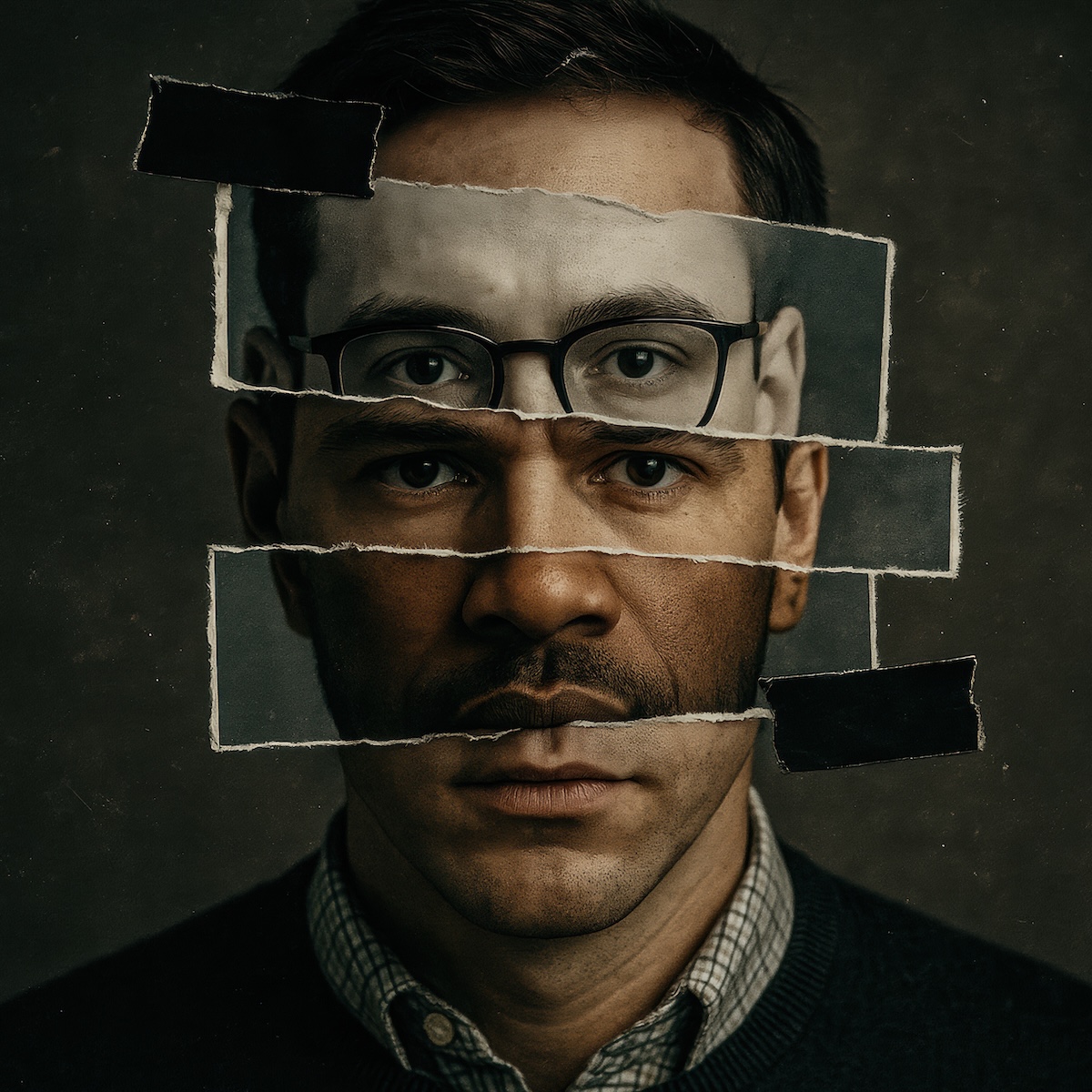
- Creating synthetic identities: Using stolen data, they manufactured fake IDs and email accounts to flawlessly impersonate property owners.
- Gathering intelligence: They pulled title reports to map out encumbrances and calculate their exact potential payout.
- Fabricating paper trails: The criminals backed up their lies with forged bank statements, leases, and fake death certificates.
- Exploiting the gaps: They went after private hard money lenders to take advantage of less standardized underwriting processes.
Why the eye test fails
This scheme worked purely because it looked real. When a fraudster hands over a high-quality fake ID and emails from an account matching the owner's name, a manual visual check falls flat.
ALTA recently updated its Best Practices for exactly this reason. Identity verification has become the absolute most critical control point in any real estate deal.
Defending transactions with Proof
Basic identity checks are officially insufficient. To stop transaction-level infiltration, title agents need a defense strategy built entirely on hard evidence and cryptographic certainty. Here is how Proof protects agents, lenders, and homeowners.
Forensic identity verification (IDV)
The L.A. fraudsters relied on fake IDs designed to pass the human eye test. Proof goes deeper. Our platform uses forensic-level analysis to verify government-issued IDs in seconds. We catch the sophisticated forgeries that easily slip past a manual review.
Biometric liveness checks
A glaring red flag in this scheme was owners who were mysteriously unavailable to appear in person. Proof requires a live biometric scan. We ensure the person behind the screen is a living human whose face matches the provided ID, stopping imposters in their tracks.
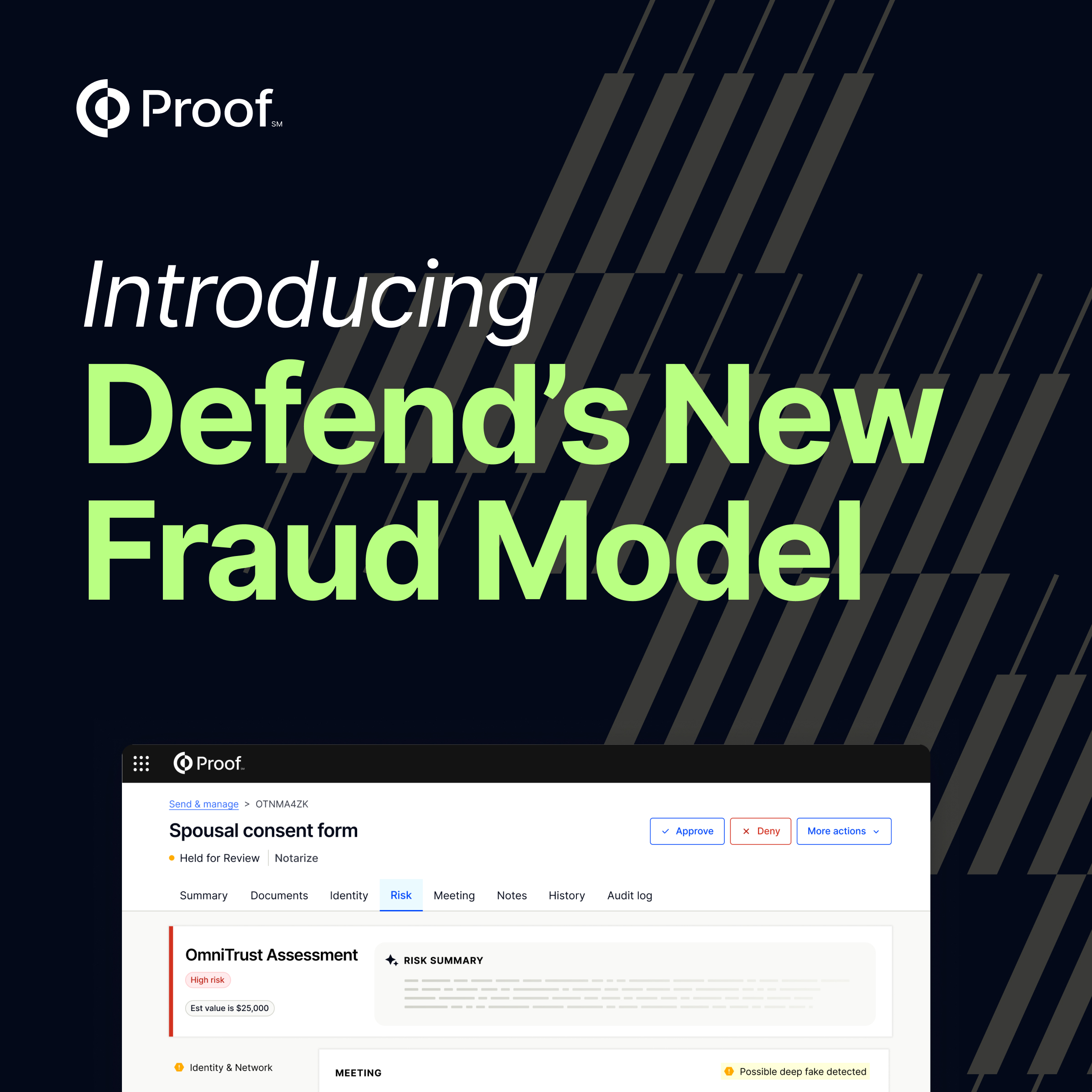
Risk scoring and fraud intelligence
Proof evaluates the complete session context alongside the document itself. By analyzing device reputation and network signals, we identify the exact patterns of newly created contact info and shell accounts that defined this $17 million heist.
Securing the human element
Fraud thrives on manufactured urgency. Moving verification into a secure and standardized digital environment removes social pressure from the title agent. The burden of proof shifts to a rigorous, evidence-based system.
Don’t let your next transaction become a headline
Criminals are shifting toward full-scale transaction infiltration, meaning your defense strategy must evolve alongside them. The latest ALTA Best Practices demand enhanced verification and greater scrutiny of remote transactions.
Protect your agency and your clients from the devastating fallout of mortgage fraud with a platform built to exceed those standards.
Request a demo to see how you can stop the next wave of transaction fraud dead in its tracks >











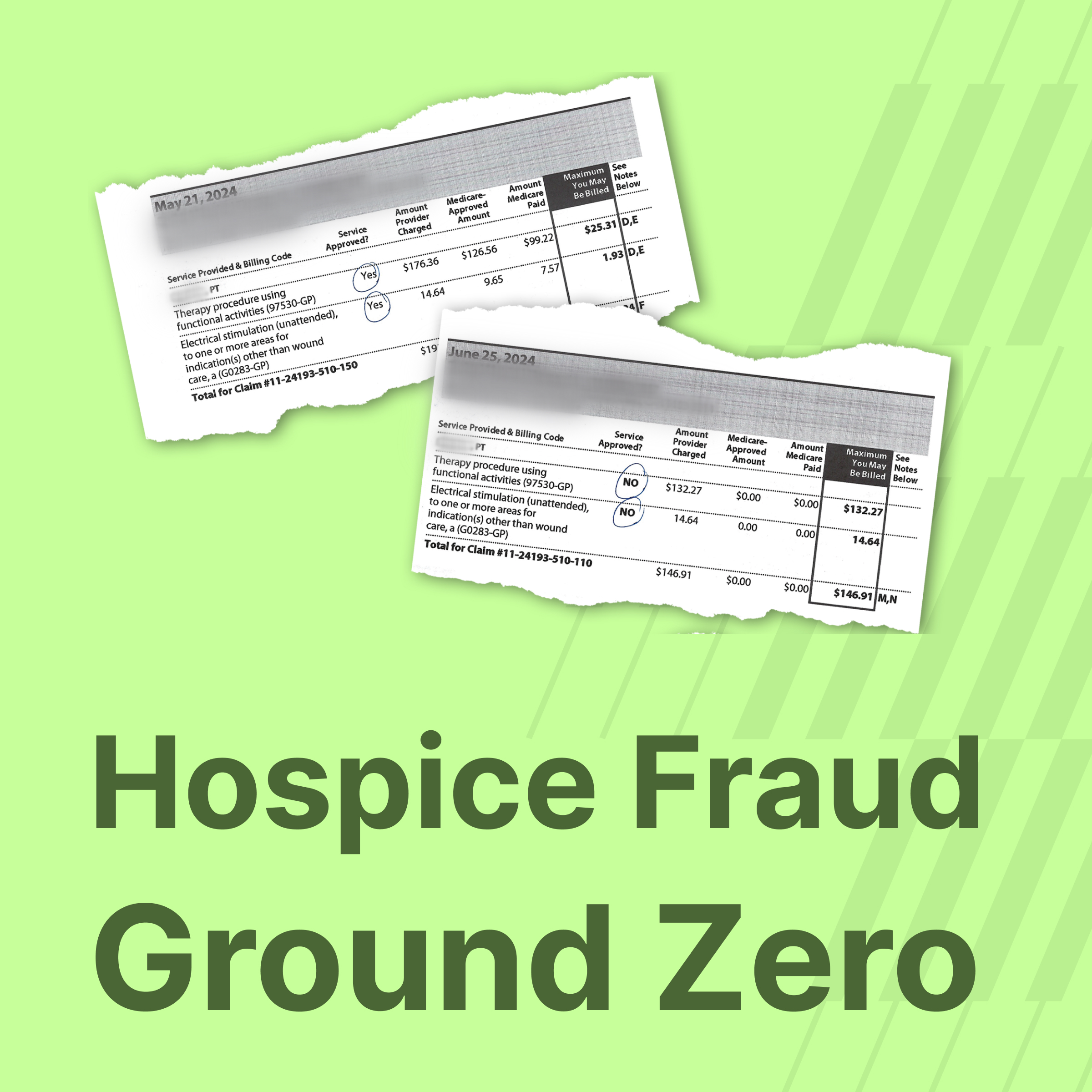
.jpg)








































































.png)

.jpg)