SaaS Security Has an Identity Problem

For years, SaaS security has focused on authentication.
Passwords. MFA. SSO. Device checks. Those controls answer one question: Is this the same credential as before?
But when something goes wrong inside a SaaS product, that is rarely the question teams actually need answered. They need to know who performed the action.
Who changed the billing plan.
Who promoted the account to admin.
Who reset the login credentials.
Who created the account in the first place.
Across SaaS, that gap between authentication and real identity is becoming one of the biggest operational risks platforms face.
Growth made the identity problem worse
Product-led growth removed friction from software adoption. Anyone can start using a product in seconds. That accessibility is powerful. It is also attractive to attackers.
Fake signups, bot traffic, credential stuffing, and trial abuse now affect companies at every stage of growth. What begins as a security issue quickly spreads across product, support, and revenue teams.
Industry data reflects the scale of the shift.
Organizations now use nearly 100 SaaS applications on average, dramatically expanding the number of identities businesses depend on. And at the same time, stolen credentials remain one of the most common entry points in web application breaches.
For SaaS platforms, these are not isolated security problems. They directly affect how companies measure growth, protect customers, and operate the product.
Where identity breaks inside SaaS products
Authentication is widely deployed across SaaS platforms, but it was never designed to solve every trust problem inside a product. Most identity gaps appear at predictable points in the lifecycle.
Account creation
Freemium models invite experimentation. They also invite automated abuse. Digital account creation is widely recognized as one of the highest-risk moments for online fraud, with suspicious activity appearing in a meaningful share of attempts. Fake accounts distort activation metrics, consume infrastructure, and make product data harder to trust.
Account recovery
Password resets and email changes are common takeover paths. Without stronger identity signals, support teams are often left guessing which user is legitimate.
Admin permissions
A compromised user account is bad. A compromised administrator account is worse. Role changes, API key access, and environment controls are frequently protected only by login credentials.
Billing and subscription changes
Revenue risk is often overlooked in SaaS identity discussions. Unauthorized billing updates and subscription manipulation often trace back to compromised accounts rather than payment fraud.
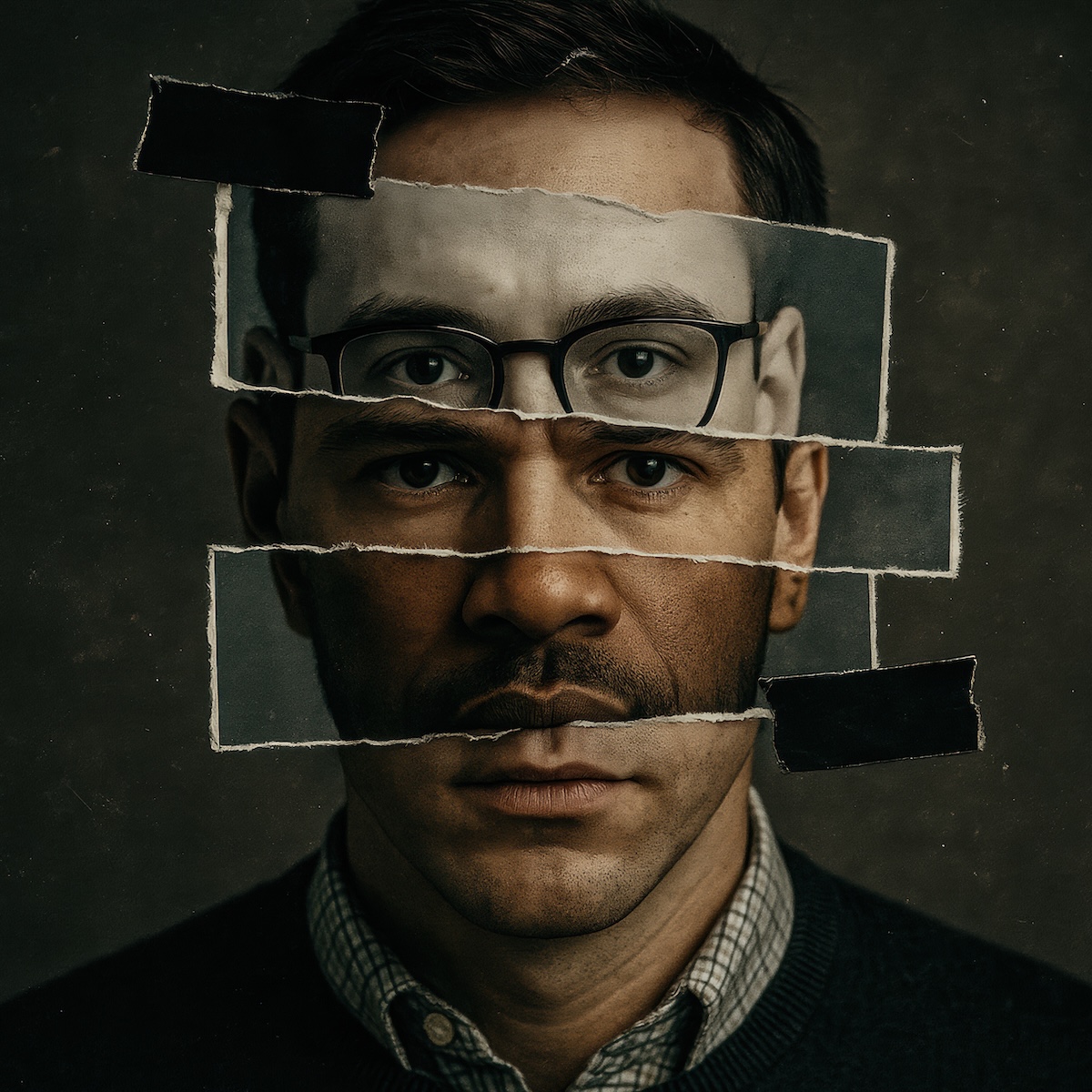
Across these moments, the pattern is the same. Authentication confirms a session. It does not confirm the person.
The operational cost of identity gaps
When identity is uncertain, the impact spreads quickly.
Growth teams lose confidence in their metrics because fake accounts inflate usage and conversion data.
Security teams investigate incidents that are difficult to prove or resolve.
Support teams spend hours working through account recovery, disputes, and escalations.
Finance teams deal with fraud losses and chargebacks tied to unauthorized activity.
Digital fraud overall continues to rise. Recent estimates suggest fraud costs businesses nearly 8% of equivalent annual revenue globally, highlighting how significant the exposure has become. For SaaS companies built around usage data and product velocity, those disruptions matter.
The challenge is not just detecting suspicious behavior. Many platforms already do that. The challenge is proving who is behind the action.
Authentication secures access. Identity secures the product.
Most security stacks in SaaS focus on protecting logins. That includes tools for authentication, risk scoring, and behavioral analysis. These systems are valuable, but they leave a gap at the exact moment teams need certainty.
Authentication confirms credentials. Identity confirms people. That distinction becomes critical when questions arise such as:
- Who authorized this billing change?
- Who generated this API key?
- Who accessed this dataset?
- Who escalated this account to admin?
When those answers rely only on login records, investigations slow down and disputes become harder to resolve. And now, SaaS platforms are starting to address this by adding identity assurance at the moments that matter most.
A new identity layer is emerging in SaaS
Forward-looking platforms are moving identity earlier and deeper into the product lifecycle. Instead of relying only on authentication events, they introduce identity verification at key decision points:
- Account signup
- Account recovery
- Admin privilege changes
- Billing updates
- Access to sensitive environments
- Security-critical workflows
This approach changes how teams operate. Fake accounts are filtered earlier. Account takeovers become harder to execute. High-risk actions are tied to a real individual rather than an anonymous credential.
It also improves the experience for legitimate users. Trust is established earlier, so fewer actions require manual review or support escalation.
Over time, identity becomes infrastructure rather than friction.
Where Proof fits
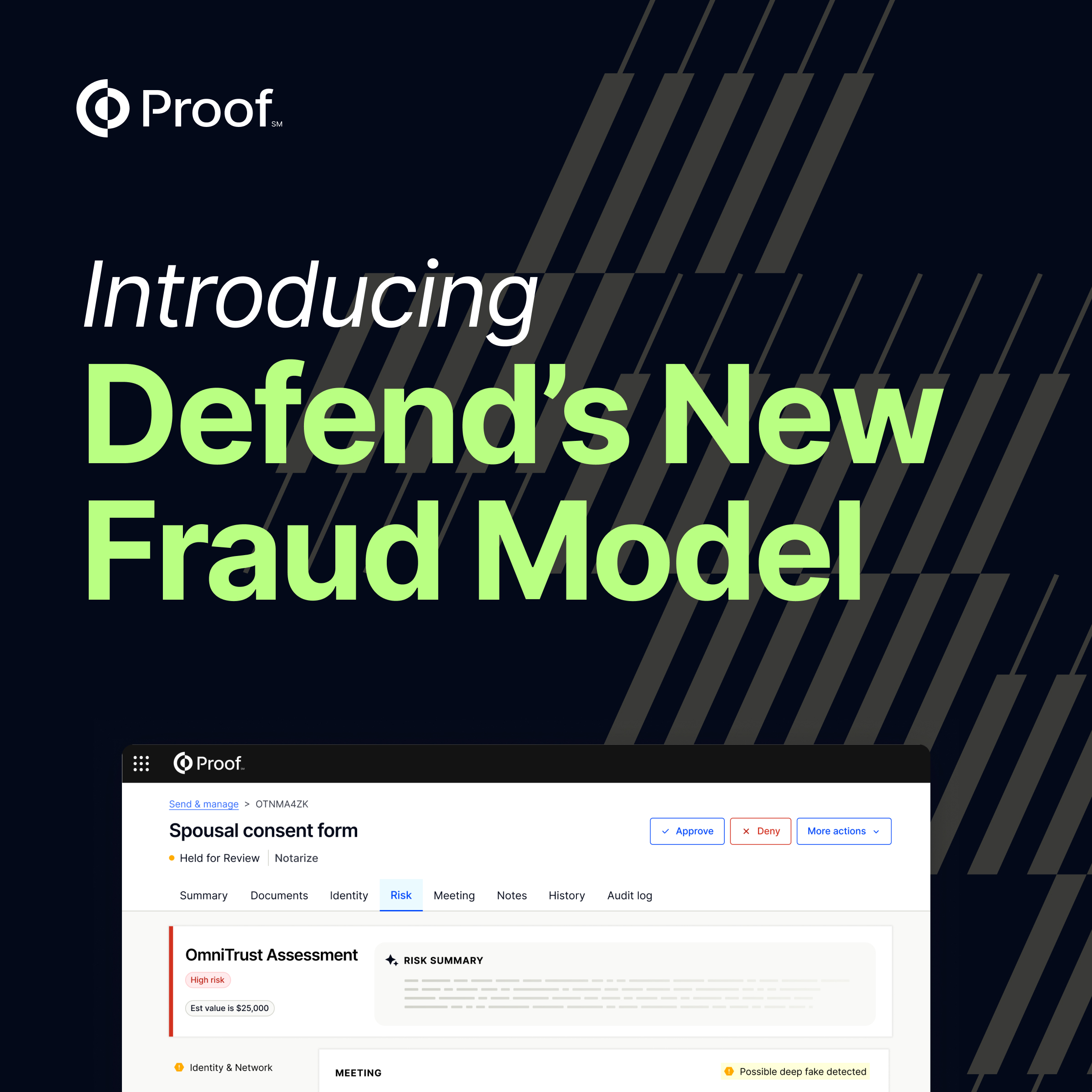
Proof helps SaaS companies close the gap between authentication and real identity.
Instead of relying solely on device signals or credentials, platforms can verify users during signup, protect account recovery, and confirm identity before sensitive actions like billing changes or administrative access. Each critical action can be tied to verified identity and recorded with clear evidence that teams can rely on later.
For SaaS companies, that means:
- Blocking fake users before they enter the product
- Reducing account takeovers and unauthorized access
- Protecting revenue tied to subscriptions and billing changes
- Giving support teams confidence when resolving disputes
- Maintaining trust without slowing down real users
In practice, Proof becomes the identity assurance layer across the SaaS lifecycle.
Identity will define the next phase of SaaS security
As SaaS ecosystems expand, the number of identities inside a product grows with them. That makes trust harder to manage and more important to prove.
Authentication will continue to play a critical role in securing access. But the platforms that scale safely will go further. They will verify the person behind critical actions and create evidence that stands up when questions arise.
Because in 2026, the real security question is no longer just whether a login was valid. It is whether you can prove who was behind it.
Learn how Proof helps SaaS platforms secure the entire user lifecycle >




















.jpg)






































































.png)

.jpg)