23 NYCRR Part 500 Is a Regulatory Shift from Authentication to Attribution
When the New York Department of Financial Services (NYDFS) updates 23 NYCRR Part 500, the changes ripple beyond compliance checklists. They reveal how regulators expect financial institutions to think about systemic risk.
23 NYCRR Part 500 applies to banks, insurers, and other financial services entities regulated by NYDFS. Its influence extends well beyond New York. Historically, NYDFS cybersecurity guidance has shaped expectations across the broader U.S. financial sector.
The amended regulation, implemented as a multi-year rollout that was completed in November 2025, strengthens requirements around multi-factor authentication, governance, breach reporting, and executive accountability. Beneath those updates is a clear message: while MFA is now a baseline requirement, identity systems built on weak MFA methods are no longer defensible.
The regulation Is about architecture, not just authentication
At a surface level, Part 500 requires covered entities to implement multi-factor authentication for access to internal systems unless they deploy reasonably equivalent or more secure compensating controls, approved by the CISO and reviewed annually.
The more important implication is architectural. For years, the financial services industry has relied on a model that treats identity as a combination of secrets: passwords, security questions, one-time codes sent via SMS, and device recognition based on cookies. Those controls were designed in an era when threat actors were less organized, less systematic, and operating at a fraction of today's scale.
That world no longer exists.
Credential theft is industrialized. Phishing kits are inexpensive. Tools to carry out adversary-in-the-middle attacks to defeat MFA are freely available open source. According to Verizon’s Data Breach Investigations Report, compromised credentials remain one of the leading vectors in confirmed breaches across industries, including financial services.
When regulators emphasize stronger authentication controls, they are acknowledging that a password-centric model supplemented with weak factors creates persistent exposure.
Identity risk extends beyond login
Many organizations are in the process of investigating or actively moving towards passwordless authentication. But eliminating password risk is not solely about improving login. It requires examining identity assurance across the full lifecycle of an account, including account creation, device enrollment, privilege changes, and crucially, account recovery.
Account recovery is often the weakest link. Many institutions still rely on knowledge-based questions or secondary channels that can be socially engineered. If an attacker can manipulate the recovery process, even strong authentication becomes irrelevant.
Most architectures authenticate sessions rather than attribute actions to verified individuals. Authentication answers whether the correct set of factors were presented. Assurance answers whether a verified person authorized the action and whether that authorization can be proven after the fact. Regulatory expectations are increasingly aligned with assurance.
23 NYCRR Part 500 signals a shift to identity assurance
The amended regulation strengthens executive certification requirements and expands expectations around access controls and governance. These updates reinforce that cybersecurity controls must withstand scrutiny, not simply exist on paper.
For financial institutions operating in New York, identity controls must be documented, defensible during regulatory review, and increasingly resistant to the phishing and social engineering attacks regulators have explicitly flagged as priority risks.
If passwords are insufficient, the solution cannot simply be more layers. It must be a stronger foundation for identity.
Financial services is moving toward models where identity is not just authenticated at login, but cryptographically bound to high-risk actions. Instead of relying on knowledge of a secret, systems must rely on proof of verified identity and tamper-evident records.
Institutions that treat password elimination as a compliance exercise will struggle to keep pace. Those that treat it as an infrastructure evolution will be better positioned for regulatory scrutiny and fraud prevention alike.
Enforcement will test evidence, not policy
What changes under the amended Part 500 is how institutions are evaluated when something goes wrong. The standard is now whether outcomes can be proven, not just whether controls were implemented.
During NYDFS investigations, institutions are required to produce evidence that explains what happened, who was involved, and how decisions were made. That evidence must stand on its own. Written policies or control descriptions are not enough without records that substantiate them.
This dynamic becomes even more acute outside of regulatory review. In account takeover disputes, the burden shifts to the institution to demonstrate that a legitimate user authorized a transaction. In civil litigation, internal system records are elevated into formal evidence and examined accordingly.
These moments expose a gap in many environments. Systems may confirm that access was granted, but they often cannot establish who actually initiated a high-risk action or whether that action was authorized by a verified individual.
Executive accountability reinforces this shift. Under the amended Part 500, senior executives must certify the effectiveness of cybersecurity controls. That certification is about whether the institution can stand behind the evidence those controls produce.
For institutions, this reframes the problem. The question is not only how to prevent unauthorized access, but how to prove, after the fact, that authorized activity was legitimate.
Building identity that meets the new regulatory standard
Regulations like 23 NYCRR Part 500 are raising the bar for what effective identity controls mean in practice. It is no longer enough to demonstrate that multi-factor authentication is deployed or that password policies meet minimum thresholds. Financial institutions must be able to show, with clarity and confidence, that high-risk actions are attributable to verified individuals and that those actions can be reconstructed and defended if challenged.
Meeting that standard requires identity that is verified at a high level of assurance and cryptographically bound to the digital actions that matter most.
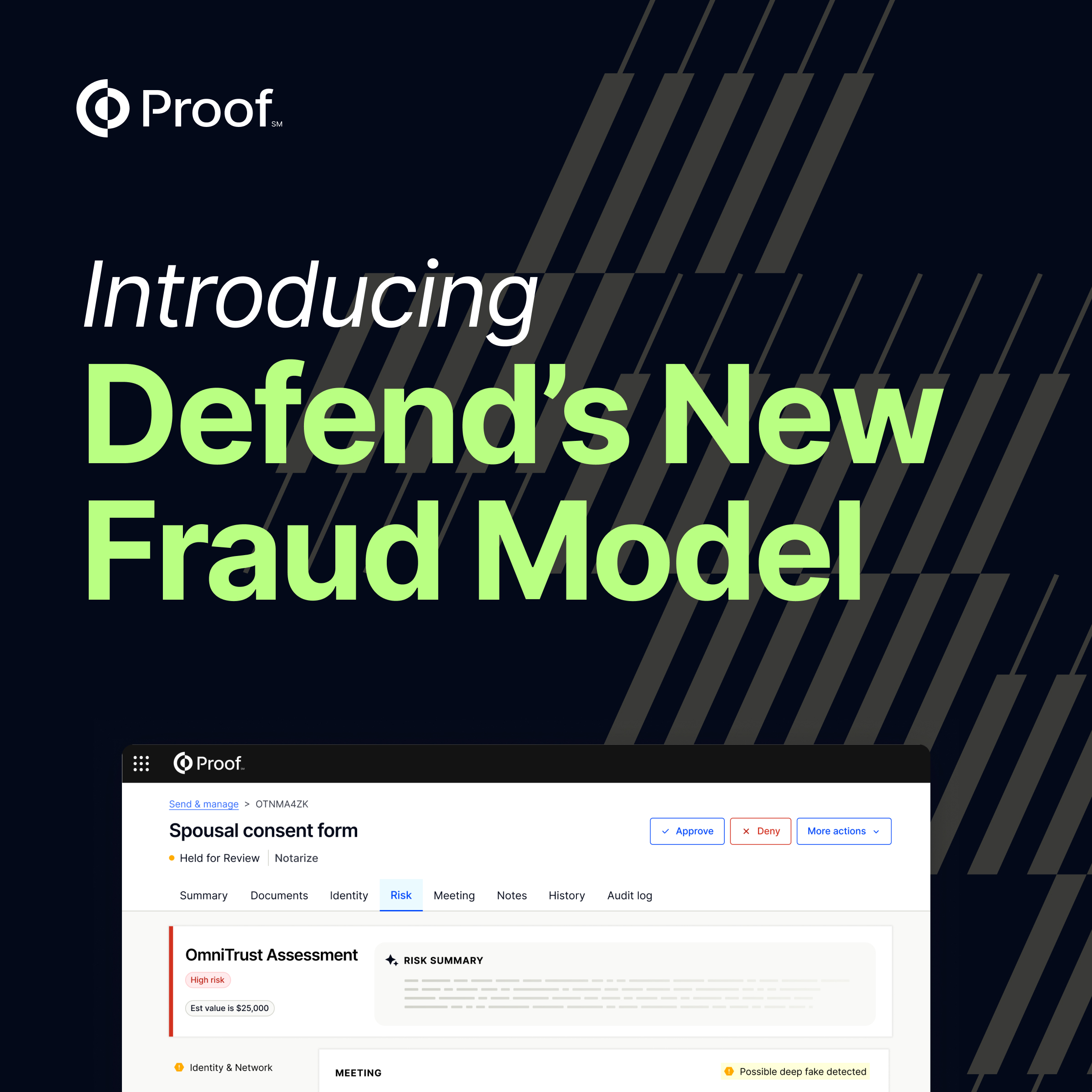
The Proof platform was built to provide that foundation. By combining identity verification with tamper-evident digital records, Proof enables institutions to tie transactions, authorizations, and account changes to a real, verified person. That evidence persists beyond the moment of access and can withstand regulatory scrutiny, internal audit, and dispute investigation.
If your institution were required tomorrow to demonstrate who authorized a high-risk transaction, a beneficiary change, or a funds transfer, could you produce cryptographic evidence tied to a verified individual? If not, your identity architecture may already be behind regulatory expectations.
23 NYCRR Part 500 is a signal that identity assurance is now a governance issue. Institutions that modernize now will reduce fraud exposure, strengthen regulatory defensibility, and certify compliance with confidence. Those that don't will be defending authentication logs when regulators ask for proof of authorization.

.jpg)

















































































.png)

.jpg)