Account Recovery: The Security Risk Hiding in Help Desk Requests

Organizations have spent the past decade strengthening employee authentication, and access to sensitive environments.
Multi-factor authentication, fully-integrated identity providers, and passwordless logins have made it harder for attackers to break into enterprise systems using brute force.
But attackers rarely attack the strongest defensive points directly. Instead, they look for the easiest path to gain access.
Increasingly, that “easy” path takes advantage of archaic employee account recovery workflows.
Password reset, IT help desk request, and device enrollment workflows exist to help employees quickly regain access when something goes wrong. Yet when these processes rely on weak or passive signals, human judgment, and knowledge-based authentication, they can quickly become one of the easiest ways for adversaries to access internal systems and bypass security protocols.
Why account recovery is becoming a target
Account recovery sits at a difficult intersection between security and productivity.
Employees forget passwords. Devices are lost, stolen, or replaced. Authentication apps stop working. Even organizations that have moved to Passkeys still need recovery processes when something goes wrong.
To keep work moving, companies design these workflows to be fast and convenient.
But that convenience creates opportunities for attackers.
Many recovery workflows still rely on signals that attackers can easily compromise or impersonate, including:
- security questions
- password reset links (possibly sent to compromised email accounts)
- one-time passcodes (intercepted, or sent to compromised devices)
- manual identity checks by help desk agents
These methods were designed for usability, not to withstand sophisticated social engineering powered by GenAI tools.
Recent incidents have shown how effective these tactics can be. Attackers have increasingly targeted corporate help desks directly, impersonating employees in order to convince IT staff to reset credentials or two-factor authentication methods. When attackers gain access to one system, they can often move laterally across internal systems.
Instead of bypassing security controls, attackers persuade someone to open the door for them.
The operational reality for IT teams
Inside most organizations, account recovery is not a rare edge case, it’s a routine operational task.
At large organizations, it’s almost guaranteed that at least one employee will encounter this issue every day.. As a result, password resets account for 20 to 50 percent of IT help desk tickets each year, according to Gartner.
Each request forces IT teams to balance two priorities.
- Quickly restoring access so employees can get back to work.
- Ensuring they aren’t granting access to someone impersonating a legitimate employee.
This tension is exactly what attackers exploit.
A convincing story, a sense of urgency, and a small amount of personal information can often persuade a support agent to issue a reset or temporary credential.
When that happens, the attacker bypasses every other security control that came before it.
Identity attacks are accelerating
The broader threat environment makes this problem even more urgent.
The IBM Cost of a Data Breach Report estimates that the average cost of a data breach in the U.S. reached a staggering $10.22 million in 2025, highlighting the growing cost of identity-driven security incidents.
At the same time, credential theft has exploded. Last year, researchers reported a dataset containing more than 16 billion leaked login records, giving attackers enormous resources for launching account takeover campaigns.
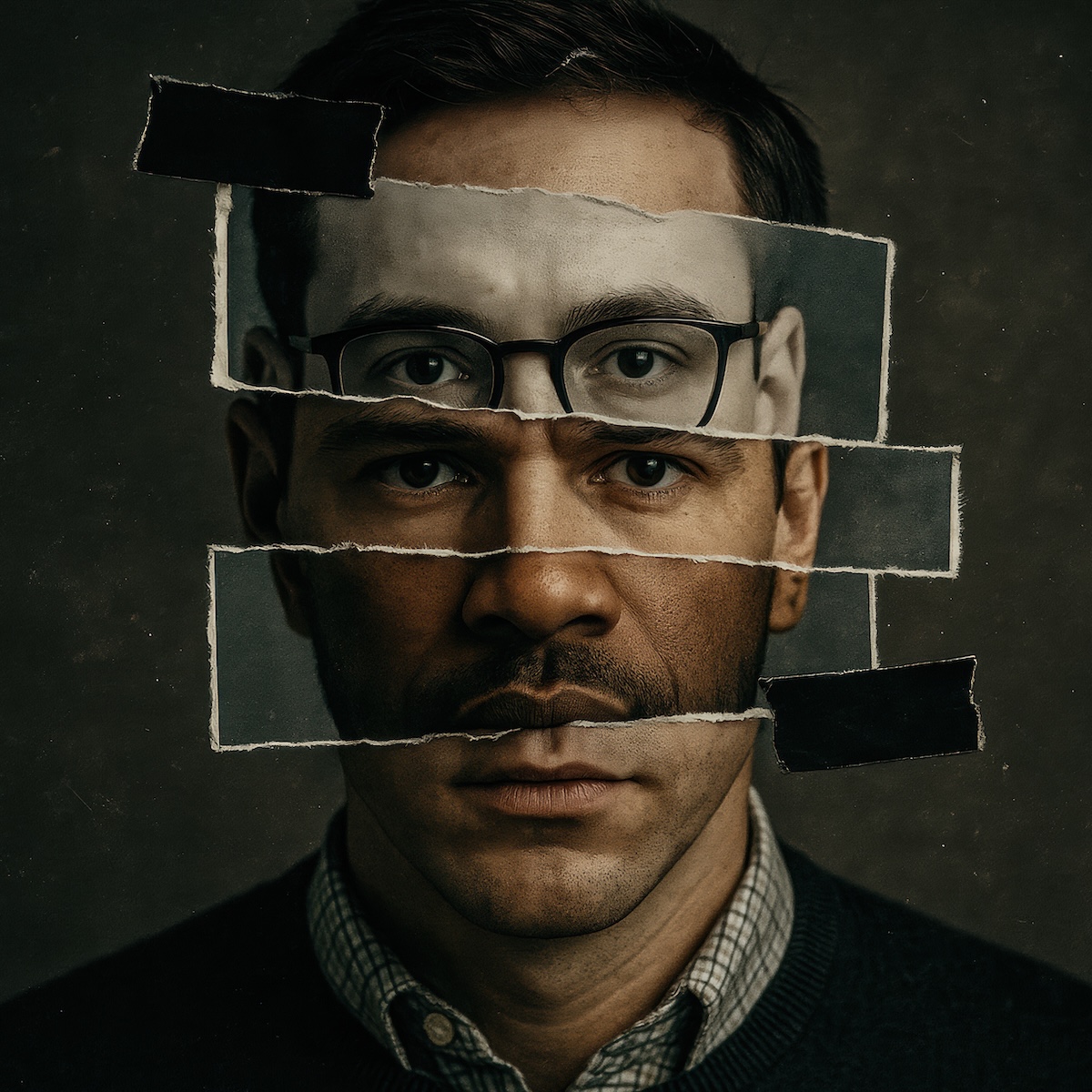
Artificial intelligence is also amplifying social engineering. Security researchers warn that generative AI tools are enabling more convincing impersonation attacks, including deepfake audio and video designed to trick support teams.
Taken together, these trends make identity the most valuable target for attackers. And account recovery is often the weakest point in that system.
A better model for account recovery
The most effective way to close this “account recovery” gap is simple: verify the identity of the person requesting access before the recovery process is completed. Instead of relying on security questions or subjective judgment, organizations can require employees to prove who they are as part of the workflow.
This approach can secure several common recovery scenarios.
Self-service password resets (SSPR)
Before issuing a reset link, the system requires employees to complete identity verification. Once verification succeeds, password resets can proceed.
Help desk-assisted recovery
When an employee contacts IT support, the help desk agent sends an identity verification link. The recovery process is initiated only after verification succeeds.
Device and MFA enrollment
When an employee is being onboarded, or needs to enroll a new device or authenticator, identity verification ensures the request is coming from the legitimate user.
This process eliminates the most vulnerable and commonly exploited step in traditional recovery workflows: subjective identity checks.
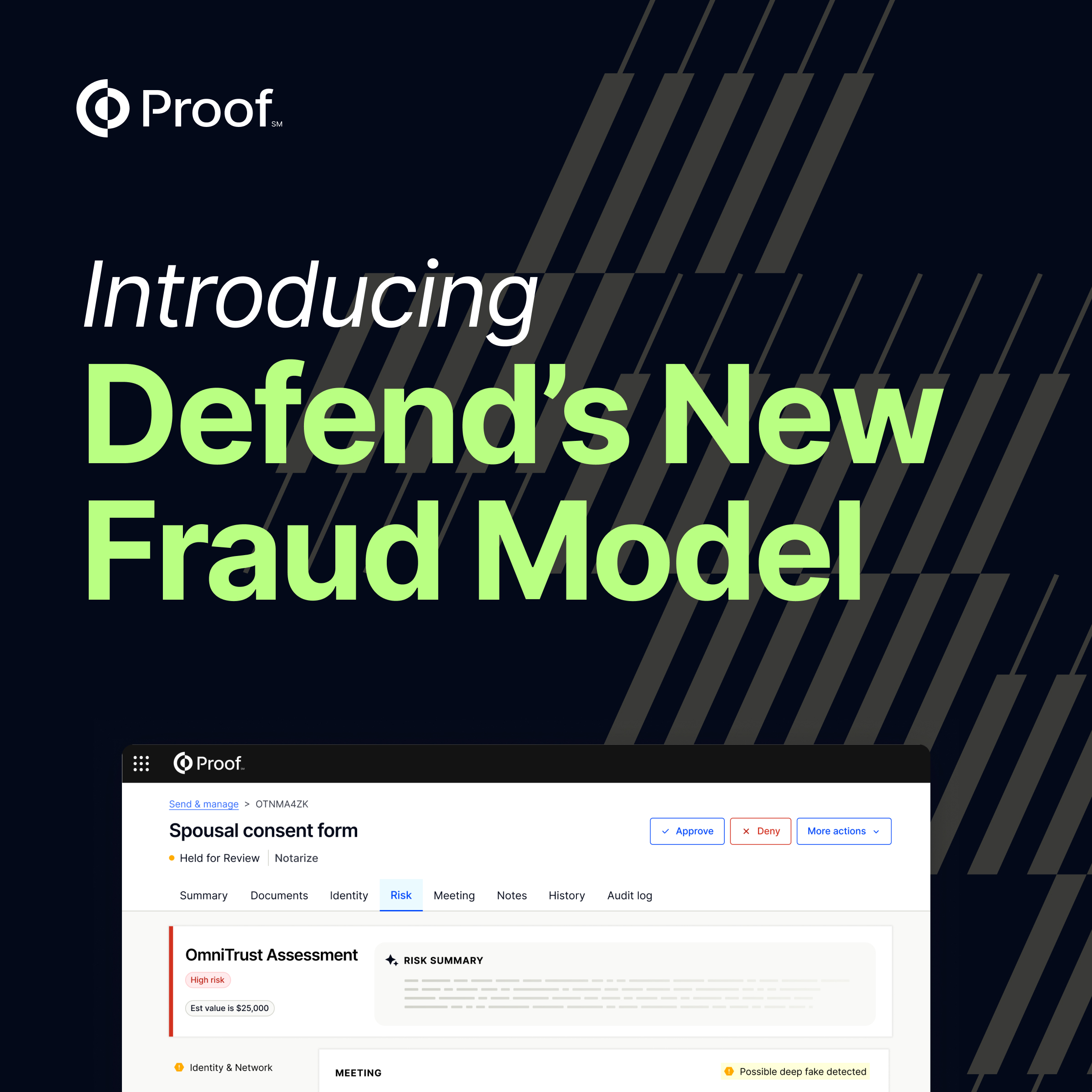
How Proof secures account recovery
Proof enables organizations to verify employee identities as part of their account recovery workflows.
By integrating identity verification with password reset systems, help desk platforms, and identity providers, organizations can ensure the person requesting access is actually an employee.
Companies use Proof to:
- Verify employee identities before password resets
- Secure help desk recovery requests
- Protect device and MFA enrollment workflows
- Detect deepfakes and impersonation attempts
- Create reusable digital identities that simplify future verification
For IT teams, this removes guesswork from recovery processes. Help desk agents don’t have to rely on intuition or incomplete identity signals. Verification becomes part of the workflow itself.
Employees benefit as well. Instead of answering security questions or waiting for manual assistance, they can complete a quick identity verification step and regain access quickly. Security gets better while the employee experience becomes faster and more reliable.
Learn how Proof protects account recovery
Proof helps organizations verify employee identities before completing password resets, help desk requests, and device enrollment. By embedding identity verification directly into recovery workflows, teams can restore access quickly while ensuring only legitimate users regain control of their accounts.
























.jpg)























































.png)

.jpg)