How To Protect Your Business From Digital Identity Fraud

Updated May 1, 2026
Digital identity fraud isn't slowing down. It's accelerating. Business identity theft is more complex than individual identity theft, the payoffs for criminals are larger, and the attack surface keeps expanding as more workflows move online. Protecting your business has always been a moving target, but the stakes have never been higher. As organizations continue facilitating digital transformation, cybercriminals are evolving just as fast.
The shift to digital transactions that began years ago is now permanent, and cybercriminals have kept pace. Every new digital channel, from online payments to remote account management, creates another entry point for fraud. The FTC reports that identity-related fraud continues to climb year over year. And because business identity theft carries potentially larger payoffs than targeting individuals, it's a growing priority for sophisticated fraud rings.
The threat is real. So are the controls. Businesses now have layered, high-assurance tools to stop identity fraud before it reaches critical workflows.
What is digital identity fraud?
Digital identity fraud is a process in which a threat actor exploits weaknesses in security to illegally obtain sensitive information and use it to commit fraud. For individuals, that means stolen social security numbers, credit card numbers, PINs, or dates of birth, data that makes up your digital identity. Criminals then use this information to open new lines of credit, apply for loans, and access other services.
But digital identity fraud also targets businesses directly. The Department of Justice's Office for Victims of Crime defines business identity theft as identity theft committed with the intent to defraud or hurt a business, including financial fraud, tax fraud, and extortion. A bad actor may use your company's EIN, credit profile, or registered identity to open accounts, file fraudulent returns, or damage your brand.
While offline identity theft has long been prevalent in some form, such as stealing a wallet, posing as a legitimate business to extract personal information, or looking through trash to obtain personal financial documents, online identity theft can be much harder to prevent and potentially gives cybercriminals access to far more sensitive information.
There are common warning signs with which most of us are now sadly familiar: receiving bills from unknown service providers, finding rogue accounts opened in your name, being notified by the IRS that more than one tax return has been filed on your behalf, or noticing odd transactions on personal or company bank statements. Each of these signals that a fraudster has found their way into a vulnerable account.
Is digital identity fraud increasing?
Yes. The FTC reports that identity-related fraud continues to climb year over year. As more business workflows move online, the attack surface expands. Sophisticated fraud rings increasingly target businesses rather than individuals because the payoffs are larger and detection can take longer. Staying ahead of the threat requires layered defenses, regular monitoring, and identity-first tools at every transaction touchpoint.
What is the business impact of digital identity theft?
Businesses are under near-constant threat of digital identity theft. A study by PWC's Global Economic Crime and Fraud Survey revealed that 46% of businesses reported experiencing fraud, digital identity theft, or other economic-related crimes in the previous 24 months.
The business impact of these cases can be severe. Among companies with global annual revenues of more than $10 billion, one in five reported a fraud incident with a financial impact of more than $50 million. And new threats continue to emerge as digital channels multiply.
Asset misappropriation, unauthorized trading, intellectual property (IP) theft, money laundering, and tax fraud are devastating businesses of all sizes.
What types of digital identity fraud target businesses?
Attackers don't pick a single method. They cycle through tactics until something works. These are the fraud types most likely to hit your business:
- Financial identity theft: This most common type of digital theft happens when a bad actor obtains financial details and uses them to apply for new lines of credit, loans, and services.
- Tax identity theft: This occurs when false tax returns are filed to claim and collect a refund.
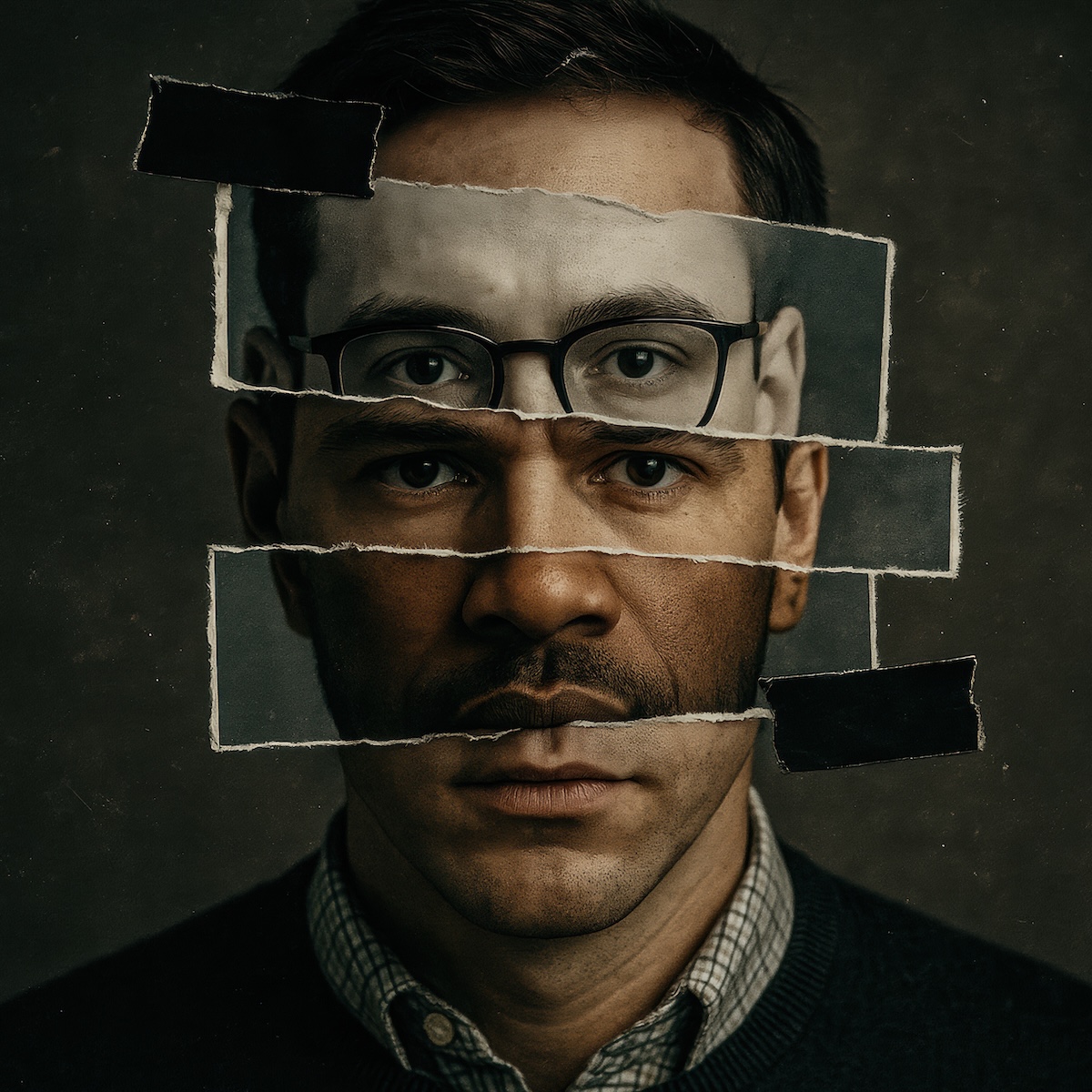
- Identity cloning: A cybercriminal illegally obtains personal information to impersonate a victim and conceal their own identity.
- Social media identity theft: A form of identity cloning in which a social media account for an individual or a brand is imitated to defraud online friends and contacts.
- Synthetic identity theft: A bad actor creates a new identity using real and fabricated personal details, such as an actual social security number combined with a fake date of birth, to evade anti-fraud systems.
- Website defacement: Criminals manipulate or hijack your business's web presence to damage your brand, spread misinformation, or redirect customers to malicious sites.
- Trademark ransom: A fraudster registers your business name or logo as an official trademark and demands payment to release it back to you.
What are the warning signs that my business has been targeted?
Watch for unexpected invoices or bills your business didn't generate, unusual account activity on business credit lines, tax notices from the IRS tied to returns your company didn't file, and complaints from vendors or customers about communications or orders they didn't initiate. Any change to your business registration records that you didn't authorize is a serious red flag that should be investigated immediately.
11 common digital identity theft tactics
Attackers don't limit themselves to a single approach. With many tactics available to them, identifying when a cybercriminal is targeting your business can be challenging. Stay alert to these common practices:
- Phishing: The sending of fraudulent messages to trick a victim into divulging sensitive information.
- Credential stuffing: The collection of usernames and passwords, most often exposed from a data breach, that are then used as credentials to access user accounts across other platforms.
- Malware attacks: A cyberattack in which unauthorized, malicious software is deployed onto an individual or business system.
- Malicious links: URLs created and distributed through spam or phishing campaigns to deploy malware on a system.
- Keystroke recording: Also known as keylogging, this cyberattack captures and records the keys struck on a keyboard to steal passwords and other sensitive information.
- Spyware: Malicious software deployed on a system that gathers sensitive information and transmits it to a third party.
- Open-source intelligence: Most often used in national security and law enforcement, OSINT involves the collection of information from publicly available sources to build a profile on a target.
- SIM jacking: Exploiting two-factor verification processes or bribing an employee at a cell phone carrier to gain control of a victim's phone number.
- Pretexting: A cybercriminal fabricates a scenario to trick a victim into handing over personal information, such as calling someone while impersonating a person in authority to extract account details.
- Email hijacking: Cybercriminals gain access to an email account by directing a victim to malicious login pages or via keylogging, then use that access to intercept communications or initiate fraudulent transactions.
- Fake social media friend requests: Created to access personal data, scrape sensitive information, or distribute malicious links.
10 ways to protect your business from digital identity fraud
Businesses now have strong, layered tools available. Here are the most effective steps to protect your organization:
1. Track online accounts
Dormant accounts can leave your sensitive information exposed. Keep a record of all your usernames, monitor your saved logins in Chrome, Firefox, and Safari, or use username and security sites to locate old accounts.
2. Invest in a password manager
Password managers make it easy to recall passwords and allow users to create hard-to-crack logins to protect from data breaches. Invest in a password manager like LastPass, Dashlane, or Keeper to maintain all your sensitive logins in one place.
3. Use multi-factor authentication
Setting up multi-factor authentication on your most sensitive accounts adds a layer of security to your login process. Even if your password is stolen, two-factor authentication makes it significantly harder for a cybercriminal to access your account.
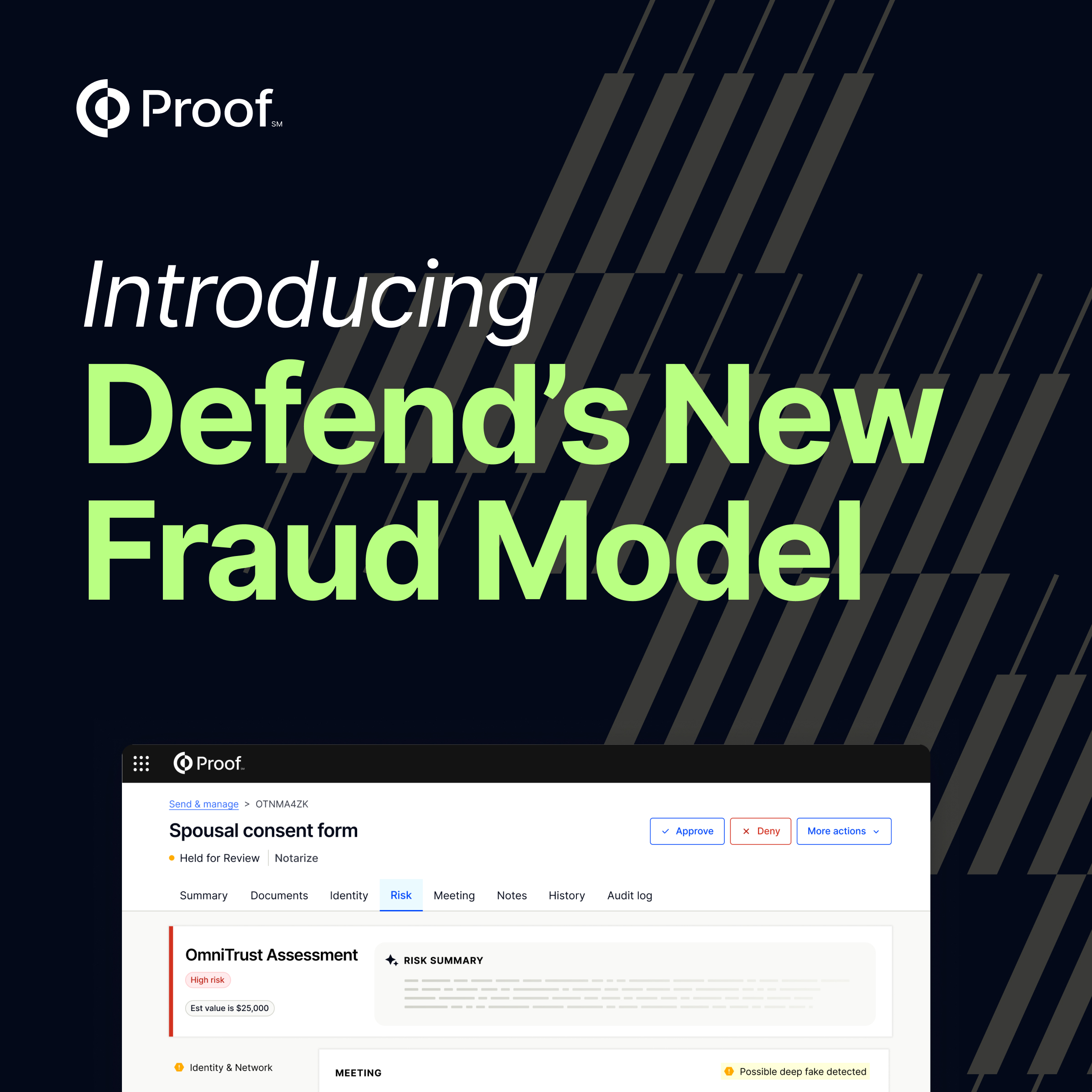
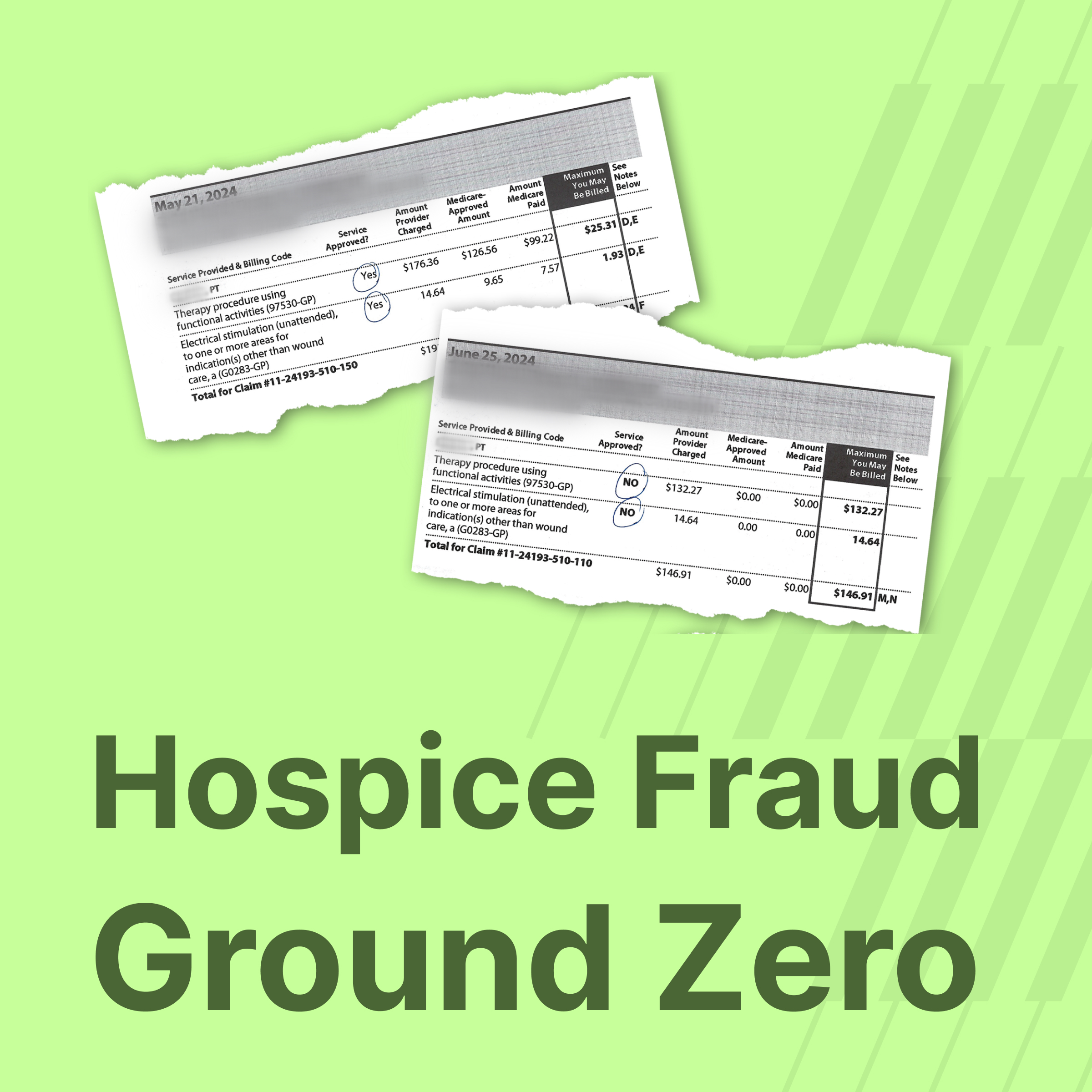
4. Switch to online notarization
Businesses can deter fraud in notarizations by adopting an online notarization process. Proof uses multiple types of verification that go well beyond the traditional notarization process, which is limited to a notary's discretion in checking a government ID.
5. Monitor bank statements
Keeping a consistent eye on your account activity helps you spot irregularities and fraudulent transactions before they compound.
6. Monitor business credit
Unlike personal credit, there is no centralized alert system for business credit. Regularly checking your company's credit report through business credit bureaus such as Dun & Bradstreet, Equifax Business, and Experian Business can surface unauthorized lines of credit or other anomalies before they do serious damage.
7. Adjust privacy settings for social media accounts
It's up to users to indicate what they want to keep private on their social media accounts. Use privacy settings to safeguard personal information and location services, and regulate your visibility to reduce what attackers can use against you.
8. Avoid downloading apps outside of official app stores
There are real risks to downloading apps from third-party stores. Outside Google and Apple app stores, many third-party providers do not conduct testing for potential malware.
9. Back up important files
Businesses need to consider having a cybersecurity recovery plan. Investing in external hard drives and cloud-based backups ensures your most important data is protected and recoverable.
10. Update software applications on your devices
Device manufacturers and app developers regularly update software to patch cybersecurity vulnerabilities. Keep your devices updated every time a new software patch becomes available, and do not let your team's personal devices fall behind.
How Proof helps protect businesses from digital identity fraud
Today, businesses are turning to Proof to help deter fraud. With notaries available 24/7, Proof has made the process of signing, notarizing, and storing documents simpler, safer, and more secure. With cloud-based hosting and a full audit trail of transactions, Proof ensures that online notarizations are protected and verifiable.
As digital identity theft techniques become more advanced, striking the right balance between client experience and fraud protection has never been more important. Proof makes it simple and safe to deliver a great user experience while also preventing identity fraud.
























.jpg)

























































.png)

.jpg)