3 Different Types of Digital Signatures and When to Use Them

Updated March 2026
Remote work and customers’ desire for digital experiences mean that organizations need to transform their business models. Embracing digital transformation means moving away from traditional, manual, and analog processes. For many companies, collecting and validating signatures remains one of the final hurdles to a completely virtual business model.
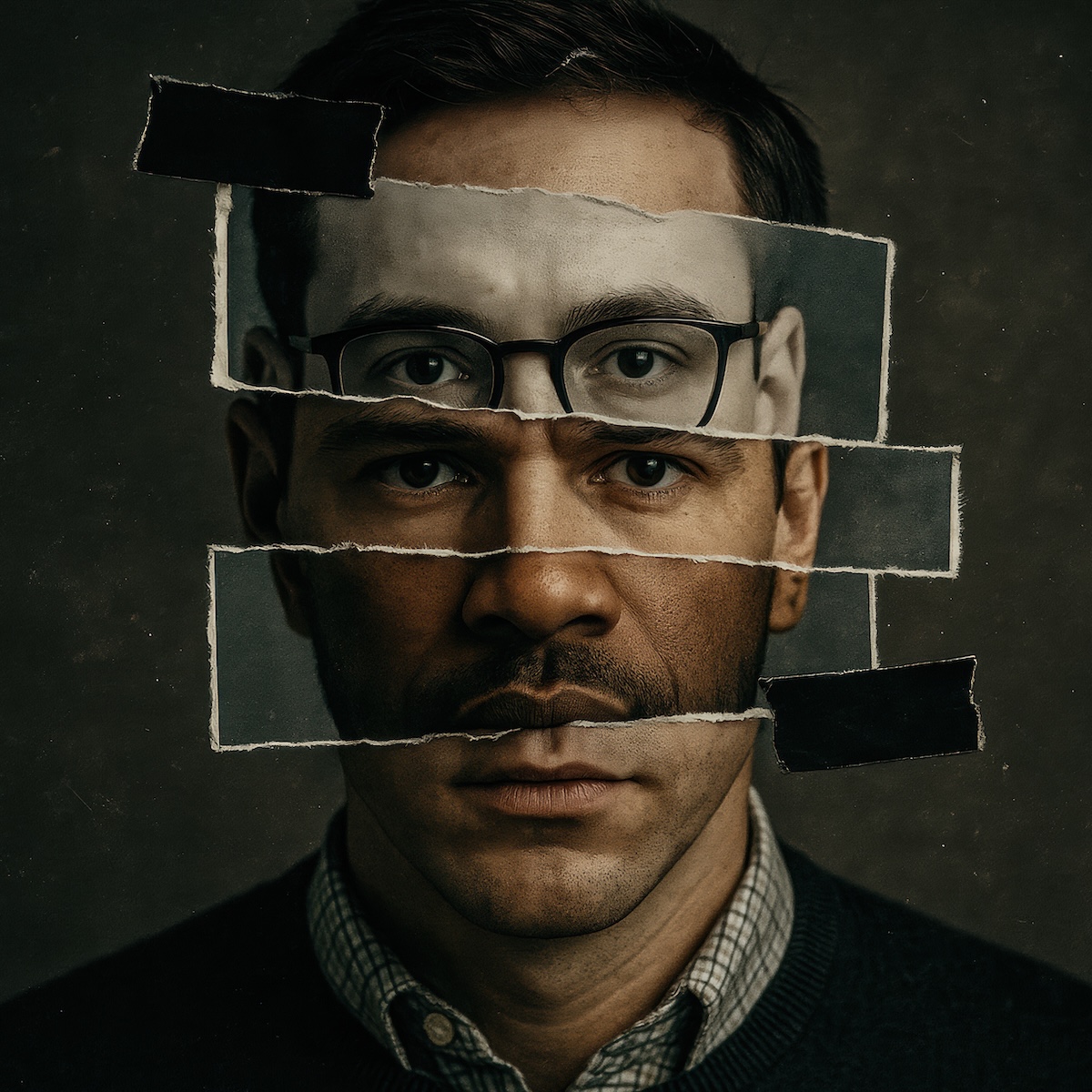
Signed documents act as a legal agreement between signees and senders, providing the assurance that both parties understand the contents. Validating the identities of the parties is fundamental to enforcing the terms and conditions contained in the documents.
With digital signatures, companies can establish legally binding documentation, but it’s important to understand the different types of signatures so they can meet their business’s legal and compliance requirements.
What is an e-signature?
Electronic signatures, or e-signatures, collect information that validates the identity of the people signing the document. Depending on the document, organizations need to consider the following when using e-signatures:
- Authenticity: Uniquely links the signature to the person
- Identity: Identifies the signatory as a real person
- Integrity: Protects the document from unauthorized changes
- Authentication: Validates that the signatory is definitely who they say they are
Some documents are more important, so the e-signature needs to meet all four requirements. In other cases, a combination of in-person knowledge or previous contact means that the type of e-signature used may not need to meet all four of the listed requirements.
In addition, geographic location and legal requirements can also impact the type of e-signature that a company uses. Some countries have strict requirements for how a company validates a signatory while others are more relaxed.
Legal Compliance and Regulatory Requirements
Organizations must understand their specific regulatory environment before implementing e-signatures. Financial services, healthcare, and real estate industries face stricter compliance requirements that often mandate advanced authentication methods. Companies operating across multiple jurisdictions need to ensure their e-signature solution meets the highest standard required in any location where they conduct business.
What is the difference between a digital and electronic signature?
When trying to remember the difference between a digital and electronic signature, it’s similar to how all squares are rectangles but not all rectangles are squares.
Electronic signatures are a broad category, like rectangles. Any signature that isn’t delivered as “wet ink,” or actual ink on physical paper, is an electronic signature.
Digital signatures rely on cryptography to lock the content and ensure that it isn’t changed after signing. They use a certificate generated by a Public Key Infrastructure (PKI). A PKI is a type of encryption that includes:
- Public key: Encrypts or “scrambles” data
- Private key: Decrypts or “unscrambles” data
The PKI ensures that only the person with the private key can access the document so that the sender can authenticate the recipient’s identity by linking it to the document and maintaining its integrity.
Security Features That Protect Digital Documents
Cryptographic signatures create an unbreakable link between the signatory and the document. This technology detects any changes made after signing—even a single character modification will invalidate the signature. Advanced systems also include timestamp verification, audit trails, and certificate validation to create a complete chain of trust that holds up in legal proceedings.
What are the three different types of electronic signatures?
Not all e-signatures have the same level of protection for authenticity, identity, integrity, and authentication. In 2016, the European Union passed the electronic Identification, Authentication, and Trust Services (eIDAS) regulation. This legal framework standardized electronic identification, signing processes, seals and documents across the EU.
The differences between the three types of e-signatures are based on the level of protection they provide.
1. Simple electronic signatures (SES)
SES is the easiest type of e-signature to manage, but it’s also the one that provides the least validation overall. An SES is basically just electronic data sent to or associated with other information that someone signs. For example, this could be a PDF that the user downloads, makes a copy of, signs, and sends back via email. These do not include a PKI.
Typically, companies use an SES in cases where they don’t need to verify a person’s identity and believe that the signature is authentic. They’re often used for low-risk documents so the recipient can acknowledge that they read and understood the document.
2. Advanced electronic signatures (AES)
An AES uses a Certificate Authority (CA) to uniquely identify the signatory and validate their identity. Usually, a company uses a delivery service provider that creates audit trails with evidence about the transaction.
A company uses AES when it needs some level of visibility and documentation across authenticity, identity, authentication and integrity.
3. Qualified electronic signatures (QES)
QES is for situations where a company must have documentation across authenticity, identity, authentication, and integrity. It provides the highest level of assurance.
This e-signature requires:
- Identification using a CA, in-person validation or video
- PKI certificate issued with appropriate technology
Although it’s the most secure e-signature, QES is also the most difficult verification method.
Choosing the Right Electronic Signature for Your Business
The decision between SES, AES, and QES depends on your risk tolerance, regulatory requirements, and the value of what you're protecting. High-stakes transactions—like real estate closings, loan agreements, or legal contracts—typically require AES or QES to ensure defensible documentation. Low-risk internal processes may work perfectly with SES, saving time and cost while still maintaining digital workflow efficiency.
Electronic signature use cases
For a document to be legally binding, a company often needs to use either AES or QES e-signatures because they are more secure and provide more documentation about the signatory.
1. Contract management
By using e-signatures for contracts, companies can digitally transform contract lifecycle management. With e-signatures, companies can send documents in bulk, track signatory completion, and integrate everything directly into a centralized repository.
2. Purchase orders
Many organizations use e-signatures as part of the procurement process. E-signatures enable organizations to ensure that the person has the appropriate signing authority to mitigate fraud risks.
3. Mortgages
Banks and lenders use e-signatures as part of the online closing (eClosing) process. As eClosings increased exponentially during the pandemic, companies learned that they save time and money. Using e-signatures for the mortgage closing legal documents is faster, more convenient, reduces errors and provides easier access to documents.
4. Claims processing
Insurance companies can pay out claims faster using digital processes, making customers happier. However, before making a payment, insurers need to validate the recipient’s identity and get legal documents signed. By using e-signatures, they can digitize the entire claims process and provide better customer service.
5. Licensing agreements
Using e-signatures for licensing agreements makes it easier for parties to document the mutual agreement over the use of branded, patented or trademarked intellectual property.
6. Legal agreements
As law firms digitally transform their business models, e-signatures have become fundamental. To enforce documents, firms need to validate and authenticate all signatories. E-signatures give them a way to streamline these processes and mitigate the risk of human error.
7. Wills, trusts and estates
Trust and estate law has always relied on signed documentation to ensure that a person’s wishes are fulfilled and that trustees meet their fiduciary duties. Usually, when a person wants to make a change to these documents, they need to sign a document in front of a witness to verify their identity. Using e-signatures can streamline these processes, making it easier for attorneys and their clients.
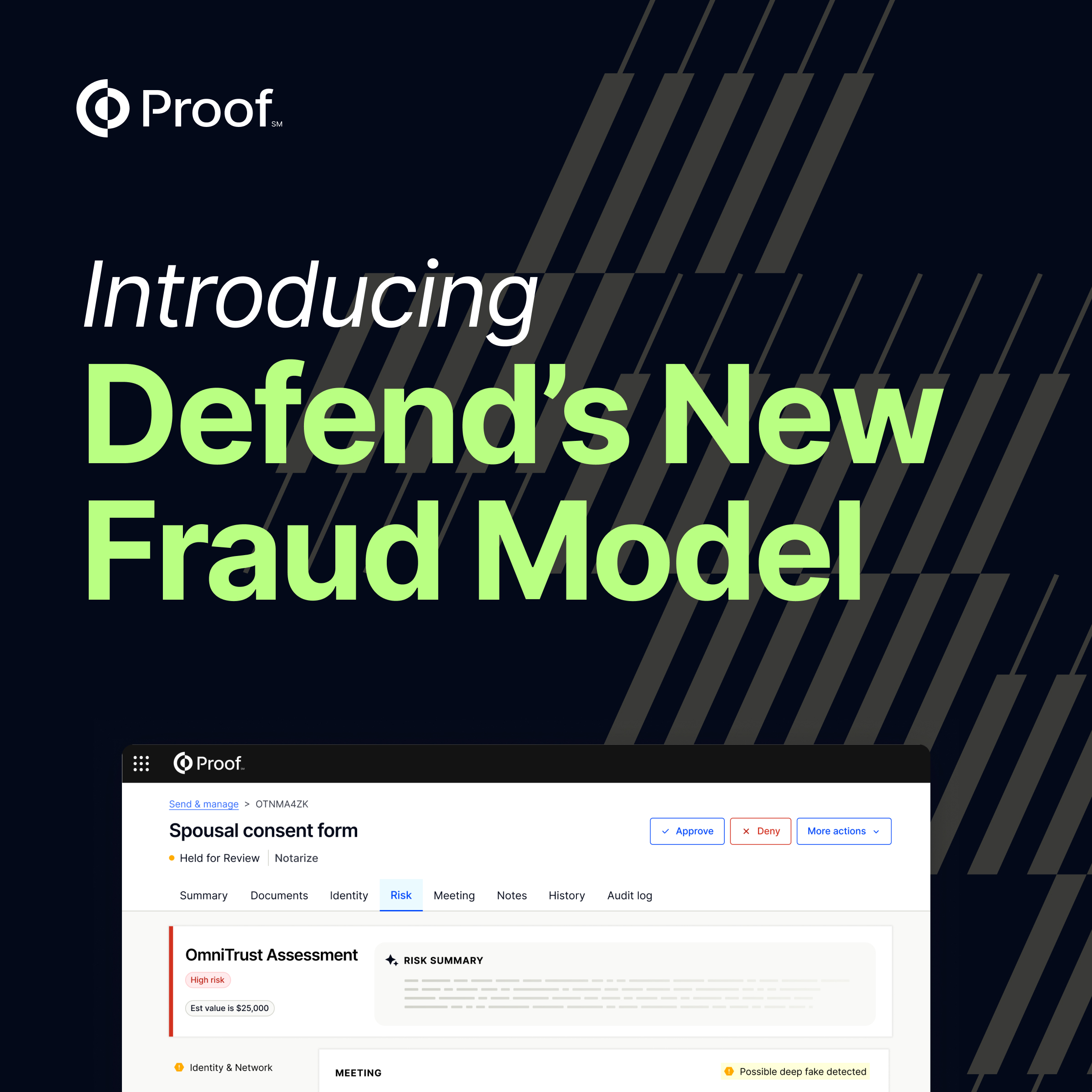
Fraud Prevention in High-Risk Industries
Financial services, real estate, and healthcare face increasing threats from sophisticated fraud attempts. Organizations in these sectors need robust identity verification and signature authentication that can detect forged documents, prevent impersonation, and create audit trails that stand up to regulatory scrutiny. Advanced e-signature platforms integrate fraud detection capabilities that analyze signing behavior, device characteristics, and document integrity in real-time.
Best Practices for Electronic Signature Implementation
Successfully deploying e-signatures requires careful planning around user experience, security policies, and compliance requirements. Start by mapping your current signing workflows to identify which documents require different levels of authentication. Establish clear policies for when to use each signature type, and ensure your platform can scale across different departments and use cases while maintaining consistent security standards.
How Notarize verifies electronic signatures
As businesses move to digital models, they need to ensure that all signatories on legal documents are verified. Using Notarize’s online notarization services, organizations can ensure the authenticity, identity, integrity, and authentication of digital signatures. Companies will also be able to monitor document completion by tracking notarizations with Notarize, which builds out a secure e-signature process.
Notarize offers 24/7 access to notaries directly from any computer, smartphone, or tablet, eliminating time-consuming travel and in-person processes. Schedule a demo to learn more about how Notarize can help your business today.























.jpg)

























































.png)

.jpg)